AI agents went from experimental to essential faster than most enterprise teams had time to plan for. OpenClaw became GitHub’s fastest-growing repository in history, reaching 247,000 stars within months of launch. It proved that a local agent connecting to messaging platforms you already use could be genuinely useful, and the market responded.
But speed of adoption exposed a serious problem. Documented malicious skills, plaintext credential storage, and full system access with no sandboxing made OpenClaw a genuine liability for enterprise use. Security teams flagged it, Meta issued an internal ban, and the pressure pushed the ecosystem to respond. NemoClaw, NanoClaw, and IronClaw each came out of that pressure, taking different approaches to the same core question: how do you get the capability of an AI agent without the risk?
This comparison breaks down all four tools across the factors that matter most for business and technical teams: what each one actually does, how they handle security, how hard they are to deploy, and which one fits your situation.
Key Takeaways
- OpenClaw is the most capable and widely used AI agent framework, but its full system access and lack of sandboxing make it unsuitable for enterprise use without additional hardening.
- NemoClaw is not a standalone agent. It is NVIDIA’s security wrapper that layers kernel-level sandboxing and policy controls on top of an existing OpenClaw deployment.
- NanoClaw runs every agent in its own Docker container with mandatory permission gates and built-in audit logging, making it the most production-ready secure option today.
- IronClaw is built in Rust with zero telemetry and Trusted Execution Environment support, making it the only framework currently purpose-built for verifiable, tamper-proof execution.
- The choice between these tools comes down to where your team sits on the security vs. speed-to-deploy spectrum, and whether you are building fresh or hardening an existing deployment.
A Quick Overview of the Leading AI Browser Agents
1. OpenClaw
OpenClaw is an open-source personal AI agent created by Peter Steinberger. It runs locally on your machine and connects to messaging platforms WhatsApp, Telegram, Slack, Discord, Teams, and more. You interact with it through channels you already use. It can browse the web, manage files, write code, schedule tasks, and run custom skills. It reached 247,000 GitHub stars in record time and became the reference framework for personal AI agents. The creator was subsequently hired by OpenAI.

2. NemoClaw
NemoClaw is NVIDIA’s enterprise security wrapper built on top of OpenClaw. Announced by Jensen Huang at GTC 2026 in March, it is not a standalone agent. It is a governance layer. It installs as a TypeScript plugin alongside OpenClaw and adds kernel-level sandboxing via NVIDIA’s OpenShell runtime, a YAML-based policy engine, and a privacy router that keeps sensitive data on local models while routing general tasks to the cloud. Think of it as a security upgrade for existing OpenClaw deployments.
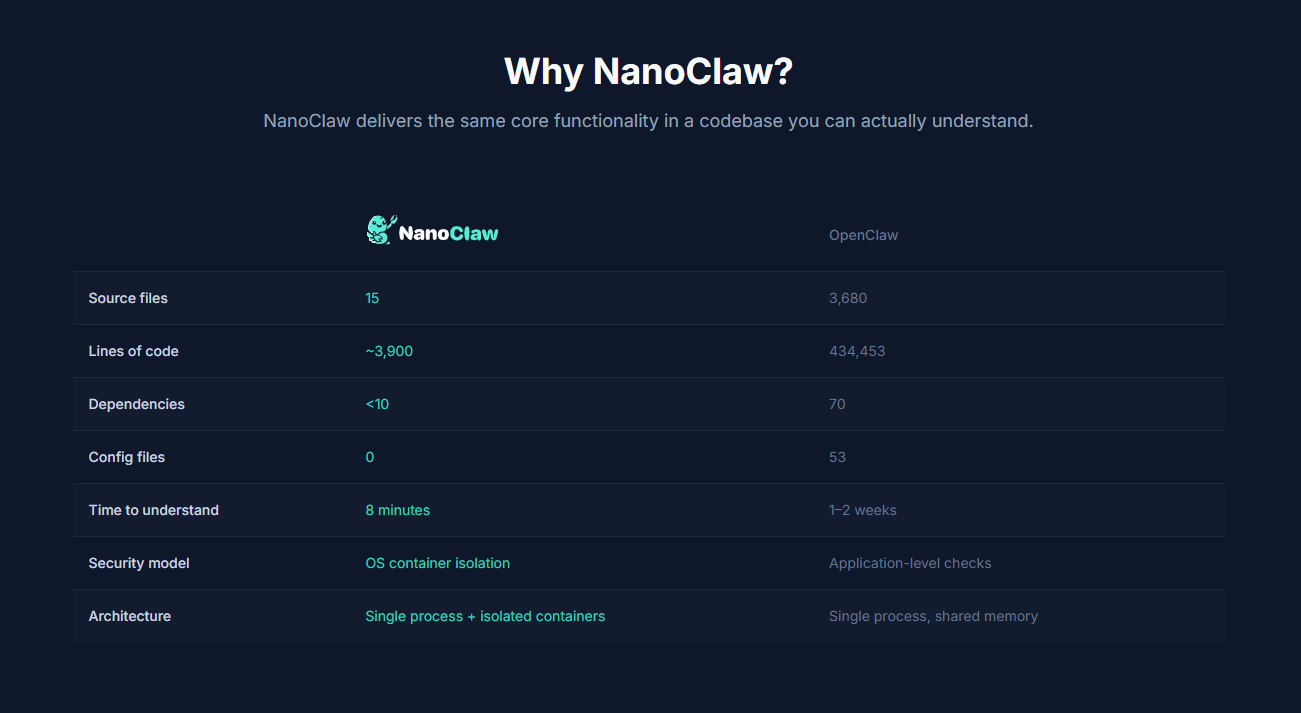
3. NanoClaw
NanoClaw takes the opposite architectural approach. Where OpenClaw has over 430,000 lines of TypeScript, NanoClaw’s entire codebase is roughly 700 lines. Every agent runs in its own sandboxed Docker container. Permission gates are mandatory. There is a built-in audit log for every action. It integrates with Anthropic’s Agents SDK and supports WhatsApp, with around 21,500 GitHub stars. The design philosophy is auditability over feature breadth.
4. IronClaw
IronClaw is an OpenClaw-inspired agent runtime rebuilt from scratch in Rust, developed by NEAR AI and announced in early 2026. Rust eliminates entire classes of memory vulnerabilities at compile time: buffer overflows, use-after-free errors, and similar issues that matter when an agent is running dozens of concurrent tool calls. IronClaw also has zero telemetry and uses Trusted Execution Environments (TEE) for verifiable execution. It was described by NEAR AI co-founder Illia Polosukhin as an agentic harness designed for security.
Here is a quick reference summary of all four tools:
| Tool | Origin | Architecture | Primary Use Case | Status |
| OpenClaw | Peter Steinberger | Monolithic TypeScript | General-purpose personal AI agent | Stable, widely used |
| NemoClaw | NVIDIA | Security wrapper on OpenClaw | Enterprise OpenClaw deployments | Early preview (March 2026) |
| NanoClaw | Community | Containerized (Docker) | Security-focused teams | Active, ~21,500 stars |
| IronClaw | NEAR AI | Rust runtime + TEE | Privacy-critical / regulated use | Early stage |
How Each Tool Handles Automation and Integrations
All four tools can automate tasks on your behalf, but they differ significantly in how they approach integrations, model support, and execution scope.
1. Automation Scope
OpenClaw has the broadest automation capability. It can interact with the file system, run shell commands, browse the web, manage calendars, send messages, write and execute code, and run scheduled background jobs. The 5,000+ community-built skills extend it further. This breadth is part of why enterprises worry about it the agent can reach almost anything on your machine.
NemoClaw inherits OpenClaw’s full automation scope but layers policy controls on top. A YAML-based engine defines what each agent can access, which tools it can call, and what data it can read. Automation is not reduced it is governed.
NanoClaw supports the core automation features messaging integrations, memory, scheduled jobs but operates within container boundaries. It connects to Anthropic’s Agents SDK natively, which makes Claude-based workflows more reliable.
IronClaw is more focused. It supports structured tool execution and multi-tool automation pipelines, and its modular architecture is designed for developers building production-grade workflows rather than general personal assistants.
2. Messaging and Channel Integrations
- OpenClaw: 20+ channels including WhatsApp, Telegram, Slack, Discord, Teams, Signal, iMessage, Matrix, and more
- NemoClaw: Inherits OpenClaw’s channel integrations, governed by its policy layer
- NanoClaw: WhatsApp and core messaging platforms; narrower but deliberate
- IronClaw: Modular channel support; fewer native integrations out of the box
3. LLM and Model Support
OpenClaw, NemoClaw, and IronClaw support multiple models via bring-your-own-key Claude, OpenAI, Gemini, and local models via Ollama. NanoClaw integrates directly with Anthropic’s Agents SDK, making it most optimized for Claude-based workflows, though it is not locked to a single provider.
OpenClaw vs NemoClaw vs NanoClaw vs IronClaw: Which One Is Easiest to Get Started With?
Setup effort and learning curve vary considerably across these tools, and the right starting point depends on your team’s technical depth.
1. OpenClaw
OpenClaw has the largest community, the most documentation, and the most tutorials. Running openclaw onboard in the terminal walks you through gateway setup, workspace, channels, and skills step by step. For developers comfortable with TypeScript and terminal environments, it is straightforward. For non-technical users, it still requires meaningful setup effort.
2. NemoClaw
NemoClaw installs as a single-command TypeScript plugin on top of an existing OpenClaw setup. If your team is already running OpenClaw, adding NemoClaw is relatively low friction. Starting from scratch means setting up OpenClaw first and then layering NemoClaw on top, which adds complexity. The YAML policy configuration also requires dedicated time from a security or DevOps team to define the right rules.
3. NanoClaw
NanoClaw is frequently cited as the fastest to get running among the security-focused options. Its codebase is small, the architecture is readable, and Docker-based setup is familiar to most development teams. You still need to be comfortable with a terminal, but it is significantly lighter than OpenClaw’s full setup.
4. IronClaw
IronClaw requires the most technical investment. Setting up TEE environments, understanding Rust-based tooling, and configuring the modular architecture takes more time. It is best suited for engineering teams with specific security requirements, rather than teams looking for fast deployment.
AI Agents: A Promising New-Era Finance Solution
Learn how AI agents are revolutionizing the finance industry by offering innovative solutions for automation, decision-making, and risk management.
Which One Can You Actually Trust With Your Data?
Security is the most important differentiator across these four tools. The risks are real: Bitdefender documented roughly 900 malicious skills in OpenClaw’s ecosystem. There have been documented cases of credential exposure and supply chain attacks. Meta issued an internal-use ban. This is what drove the creation of NemoClaw, NanoClaw, and IronClaw in the first place.
1. OpenClaw
OpenClaw gives agents full access to everything on your machine: file system, shell, credentials, installed applications. Credentials are stored in plaintext. There is no skill sandboxing. The project’s own FAQ acknowledges there is no perfectly secure setup. For enthusiasts and developers who understand what they are working with, this is acceptable. For enterprise use with sensitive data, it is a genuine risk.
2. NemoClaw
NemoClaw addresses OpenClaw’s security gaps through three mechanisms: kernel-level sandboxing via OpenShell (OS-level, not just container-level), a YAML policy engine for granular access controls per agent, and a privacy router that keeps sensitive data local. It runs on AWS, Azure, GCP, or bare metal and is hardware-agnostic. The main caveat is that NemoClaw is in early preview and has not been production-tested at scale.
3. NanoClaw
NanoClaw’s container isolation model means every chat group runs in its own sandboxed Docker container. If one agent is compromised, the blast radius is limited to that container. Permission gates are mandatory rather than optional. There is a built-in audit log. For regulated industries where compliance teams need to answer questions about what the agent accessed and when, NanoClaw’s architecture is well suited.
4. IronClaw
IronClaw’s security approach is different in kind, not just degree. Using Rust eliminates memory safety vulnerabilities at compile time. TEE support provides verifiable execution, meaning you can prove to an auditor that the code ran without tampering. Zero telemetry means no data leaves the environment involuntarily. For organizations where verifiable execution is a regulatory requirement, IronClaw is currently the only framework purpose-built for it.
Pros and Cons of Each Tool for Enterprise Teams
| Tool | Pros | Cons |
| OpenClaw | Largest ecosystem (5,000+ skills), 20+ messaging integrations, multi-model support, MIT open-source, strong community documentation | Full system access with no sandboxing, plaintext credential storage, documented malicious skills and exposed instances, 430,000+ line codebase is hard to audit |
| NanoClaw | Container isolation per agent, mandatory permission gates, built-in audit logging, small auditable codebase (~700 lines), native Anthropic Agents SDK support | Smaller ecosystem, fewer messaging integrations, most optimized for Claude-based workflows |
| NemoClaw | Adds enterprise security on top of OpenClaw without migration, kernel-level sandboxing, YAML policy engine, privacy router for data residency, backed by NVIDIA, hardware-agnostic | Early preview only, requires OpenClaw as prerequisite, policy setup needs dedicated DevOps time, adds operational overhead |
| IronClaw | Rust memory safety eliminates vulnerability classes at compile time, zero telemetry, TEE verifiable execution, purpose-built for regulated environments | Small adoption footprint, TEE limits deployment flexibility, steepest setup and learning curve, earliest stage of the four |
Which Tool Should You Choose for Your Business?
The right choice depends on your use case, your team’s risk tolerance, and how far along your agent deployment is. There is no universal answer, but the decision points are clear once you know what you are actually optimizing for.
1. Developers and Technical Teams Exploring AI Agents
OpenClaw is the natural starting point for most teams. It has the most resources, the largest skill library, and the fastest path from installation to a working agent. The community is active, documentation is extensive, and the 5,000+ skill ecosystem means most use cases are already covered. Treat the security warnings seriously, avoid exposing the gateway publicly, and review any third-party skill before installing it.
2. Teams That Need Security Without Starting Over
NemoClaw is built precisely for this scenario. If your team has already invested months in OpenClaw, building custom skills, configuring messaging channels, and tuning agent behaviors, NemoClaw adds a security layer without requiring you to rebuild from scratch. It brings kernel-level sandboxing, a YAML policy engine, and a privacy router to your existing setup. The main consideration is that it is still in early preview, so weigh that maturity gap carefully against your risk tolerance for production workloads.
3. Regulated Industries and Compliance-Driven Organizations
NanoClaw is the strongest choice for teams that need production readiness alongside security. Container isolation, mandatory permission gates, and built-in audit logs cover the three things most compliance teams ask for first. Every agent action is logged, every access point is gated, and the architecture is small enough to audit line by line. The smaller ecosystem is a real tradeoff, but for organizations that need to document exactly what the agent accessed and when, NanoClaw gives you that record.
4. Organizations Where Verifiable Execution Is a Hard Requirement
IronClaw is the only framework currently purpose-built for TEE-based verifiable execution. Built in Rust with zero telemetry, it eliminates entire classes of memory vulnerabilities at compile time and gives compliance teams provable assurance that code ran without tampering. The adoption footprint is still small and setup demands senior engineering investment. For organizations operating under strict regulatory mandates where proof of execution integrity is non-negotiable, IronClaw is the right option and worth tracking closely as it matures.
OpenClaw vs NemoClaw vs NanoClaw vs IronClaw: Final Verdict
The four tools are not really competing for the same user. They reflect different stages of organizational maturity and different risk tolerances.
OpenClaw remains the reference framework and the entry point for most teams. NanoClaw is the most mature secure alternative and the best choice for teams that need compliance-grade logging today. NemoClaw is promising for organizations with deep OpenClaw investment, but its early-preview status means it needs time to prove itself in production. IronClaw serves a specific and important niche: teams where verifiable, tamper-proof execution is a regulatory requirement. Knowing which category your organization falls into makes the decision clear.
| Category | Best Option | Why |
| Best overall for getting started | OpenClaw | Largest ecosystem, fastest deployment, widest channel support |
| Best for security-conscious teams | NanoClaw | Container isolation, audit logging, production-ready |
| Best for existing OpenClaw users who need enterprise compliance | NemoClaw | Adds governance without migration cost |
| Best for regulated / high-security environments | IronClaw | Rust safety + TEE verifiable execution, zero telemetry |
| Best lightweight option | NanoClaw | 700-line codebase, auditable, fast to deploy |
How Kanerika Helps Enterprises Deploy AI Agents the Right Way
Kanerika helps businesses rethink how they operate through applied AI. As a top-rated AI solutions company, Kanerika builds intelligent systems and deploys custom AI models with a track record of measurable results across industries. The work spans optimizing operations, sharpening decision-making, and opening up new growth opportunities. From automating workflows to solving complex operational challenges, every solution is built around the specific needs of the business.
The capability set covers AI strategy, predictive modeling, intelligent automation, marketing workflow optimization, data engineering, and low-code development. Kanerika helps organizations forecast trends, understand customer behavior, streamline operations, and manage cloud and hybrid environments with strong governance in place. ISO 9001, ISO 27001, and ISO 27701 certifications mean security and privacy are built into every engagement, not added as an afterthought.
Kanerika’s enterprise AI agents – DokGPT, Jennifer, Alan, Susan, Karl, Mike, and Jarvis – are built for document intelligence, risk assessment, customer insights, and voice analytics. Each agent is designed for scale, trained on structured enterprise data, and built to integrate into existing systems without disruption. Together they help businesses modernize operations and extract tangible value from their AI investments.
Build smarter AI agents that act and decide for you
Partner with Kanerika for Expert AI implementation Services
Case Study: Enabling Real-Time Compliance Through an AI Agent for a Global Knowledge Management Leader
Challenges
A global knowledge management firm was spending significant time on manual research across websites and social media, creating growing ticket backlogs as teams struggled to keep up. Compliance clearances were taking too long, pushing back event schedules and frustrating stakeholders. Inconsistent review processes also raised the risk of missing critical findings altogether.
Solutions
Kanerika built an AI compliance agent that automates expert profiling by connecting to internal databases and pulling relevant vetting attributes. The solution included intelligent web scraping with keyword-based search to scan news articles, social mentions, and professional records. Structured reports with citations and compliance mapping were generated automatically, evaluating findings against predefined disqualification criteria.
Outcomes
- 3X faster expert vetting
- 40% reduction in event delays
- 70% decrease in backlog cases
The Bottom Line
The “claw” ecosystem is still young, and all four tools are moving fast. OpenClaw remains the most capable starting point, but it was never designed with production security in mind. NemoClaw, NanoClaw, and IronClaw each fill a real gap that OpenClaw left open.
If you are exploring AI agents for the first time, OpenClaw gets you there fastest. If you are building something that touches real credentials, sensitive files, or enterprise workflows, the security model matters as much as the feature list. That is when NanoClaw, NemoClaw, or IronClaw becomes the more honest choice.
The right tool is the one that matches both what you need to automate and how much you can afford to expose.
FAQs
What is the difference between OpenClaw and NemoClaw?
OpenClaw is a community-driven, permissive-license framework optimized for flexibility and rapid prototyping, while NemoClaw is NVIDIA’s performance-focused variant built for GPU-accelerated inference at scale. OpenClaw offers broader customization options and integrates easily with diverse tech stacks, whereas NemoClaw delivers superior throughput on NVIDIA hardware with optimized CUDA kernels. Organizations choosing between these AI agent frameworks should evaluate their infrastructure requirements and performance benchmarks. Kanerika helps enterprises assess both frameworks against production workloads—connect with our team for a tailored comparison.
Is NanoClaw better than OpenClaw?
NanoClaw outperforms OpenClaw in resource-constrained environments where memory efficiency and edge deployment matter most. Its lightweight architecture reduces model footprint by up to 60% compared to standard OpenClaw implementations, making it ideal for embedded systems and IoT applications. However, OpenClaw remains superior for complex enterprise workflows requiring extensive plugin ecosystems and multi-agent orchestration. The better choice depends entirely on your deployment context and scalability requirements. Kanerika’s AI specialists evaluate your infrastructure constraints to recommend the optimal Claw framework—schedule a discovery call today.
What is the main difference between OpenClaw and NanoClaw for enterprise AI agent deployment?
OpenClaw prioritizes extensibility and enterprise integration capabilities with robust API connectors and workflow orchestration features, while NanoClaw focuses on computational efficiency for distributed edge deployments. For enterprise AI agent deployment, OpenClaw handles complex multi-step reasoning chains better, whereas NanoClaw excels when deploying hundreds of lightweight agents across distributed infrastructure. OpenClaw’s plugin architecture supports deeper ERP and CRM integrations out of the box. Kanerika architects enterprise AI agent solutions using the framework best suited to your operational scale—reach out for a technical assessment.
Is there a safer alternative to OpenClaw?
IronClaw is the safest alternative to OpenClaw, purpose-built with enterprise-grade security controls including mandatory access policies, encrypted agent communication, and comprehensive audit logging. Unlike OpenClaw’s permissive defaults, IronClaw enforces zero-trust principles and integrates with SIEM platforms natively. Organizations handling sensitive data or operating under strict compliance mandates benefit from IronClaw’s hardened runtime environment and granular permission models. NanoClaw also offers improved sandboxing over standard OpenClaw implementations. Kanerika implements secure AI agent frameworks with compliance-first architecture—contact us to evaluate IronClaw for your environment.
Which Claw framework is best for regulated industries like financial services or healthcare?
IronClaw is the optimal choice for regulated industries including financial services and healthcare due to its built-in compliance controls, HIPAA-ready configurations, and SOC 2-aligned audit trails. Its deterministic execution model ensures reproducible agent behavior critical for regulatory documentation, while encrypted inter-agent communication satisfies data protection requirements. IronClaw also supports granular role-based access controls essential for segregation of duties in financial workflows. OpenClaw can work with significant hardening but requires substantial customization. Kanerika deploys compliant AI agent solutions for regulated enterprises—let us design your governance framework.
Can OpenClaw be hardened to match IronClaw's security model?
OpenClaw can be hardened significantly but cannot fully match IronClaw’s security model without substantial engineering effort. You can implement TLS encryption, add authentication layers, and deploy custom sandboxing, yet IronClaw’s security is architecturally integrated rather than bolted on. IronClaw’s mandatory access controls, cryptographic agent attestation, and tamper-evident logging are native features that would require extensive custom development in OpenClaw. For organizations with strict security requirements, hardening OpenClaw typically costs more than adopting IronClaw directly. Kanerika helps enterprises evaluate build-versus-buy security decisions—request a security architecture review.
How complex is migrating from OpenClaw to NanoClaw or IronClaw?
Migrating from OpenClaw to NanoClaw is moderately complex, requiring agent refactoring to accommodate NanoClaw’s streamlined API and memory optimization patterns. Migration to IronClaw involves greater complexity due to its stricter security model, mandatory policy definitions, and different permission structures. Both migrations typically require rewriting custom plugins and updating orchestration logic. Expect four to eight weeks for NanoClaw migrations and eight to twelve weeks for IronClaw transitions depending on agent complexity and integration depth. Kanerika’s migration accelerators reduce Claw framework transitions by 40%—talk to our team about your migration roadmap.
What is the best OpenClaw variant?
The best OpenClaw variant depends on your deployment priorities. NemoClaw excels for GPU-intensive workloads requiring maximum inference throughput on NVIDIA infrastructure. NanoClaw is superior for edge computing and resource-limited environments where memory efficiency matters most. IronClaw leads for security-critical and compliance-heavy deployments in regulated industries. Standard OpenClaw remains ideal for general-purpose enterprise automation with maximum flexibility and community support. Each variant optimizes for different production constraints rather than being universally superior. Kanerika evaluates your workload characteristics to recommend the right OpenClaw variant—book a consultation to find your fit.
Is NemoClaw open source?
NemoClaw is partially open source under NVIDIA’s modified Apache 2.0 license with additional terms governing commercial GPU deployment. The core framework and inference runtime are freely available, but certain performance-optimized components and enterprise management tools require NVIDIA AI Enterprise licensing. This differs from OpenClaw’s fully permissive MIT license and IronClaw’s source-available enterprise model. Organizations can prototype and develop with NemoClaw freely but should review licensing implications before production deployment at scale. Kanerika navigates open source AI licensing complexities for enterprises—connect with us to clarify your compliance requirements.
Do I need a GPU to run NemoClaw in production?
NemoClaw technically runs on CPU-only infrastructure but loses its primary performance advantages without NVIDIA GPUs. Production deployments benefit most from A100, H100, or L40S accelerators where NemoClaw’s CUDA-optimized kernels deliver five to ten times throughput improvements over CPU inference. Running NemoClaw without GPUs makes it comparable to standard OpenClaw performance, negating the reason to choose it. For CPU-focused deployments, NanoClaw or OpenClaw offer better optimization. Kanerika designs AI infrastructure architectures matching your hardware investments—reach out for GPU optimization guidance.
What are the benefits of NemoClaw?
NemoClaw delivers exceptional inference speed on NVIDIA hardware through deeply optimized CUDA kernels and TensorRT integration, achieving throughput levels unmatched by other Claw variants. Its benefits include native multi-GPU scaling, efficient batch processing for high-concurrency workloads, and seamless integration with NVIDIA’s AI Enterprise ecosystem. NemoClaw also provides built-in model quantization tools and memory optimization features that reduce operational costs at scale. Organizations running intensive AI agent workloads on NVIDIA infrastructure gain measurable latency and cost advantages. Kanerika implements NemoClaw deployments optimized for your GPU infrastructure—schedule a performance benchmarking session.
Which Claw framework has the largest developer community in 2026?
OpenClaw maintains the largest developer community in 2026 with over 85,000 GitHub contributors, extensive Stack Overflow coverage, and the most third-party plugins and integrations. Its permissive licensing and early market entry created network effects that newer variants haven’t matched. NemoClaw has the fastest-growing community driven by NVIDIA’s developer ecosystem, while IronClaw’s community skews toward enterprise security professionals. NanoClaw maintains a dedicated following in edge computing circles. Community size impacts support availability, plugin ecosystems, and hiring considerations. Kanerika’s certified engineers support all major Claw frameworks—partner with us regardless of your chosen platform.