A single data breach costs companies an average of $4.88 million. For 60% of small businesses, it’s a death sentence—they close within six months of an attack.
Your customer database. Financial records. Intellectual property. Employee information. Every byte of data your organization creates, stores, or processes is a target. Hackers don’t discriminate—they attack Fortune 500 companies and local businesses with equal fervor, seeking any weakness in your digital armor.
Last year alone, 3,205 publicly reported breaches exposed the personal information of 353 million people—a 78% jump from the previous year. Naturally, data security isn’t about installing antivirus software and hoping for the best anymore. It’s a systematic approach to protecting your digital assets from creation to deletion. It means building walls that actually hold, creating access controls that work, and having a plan when—not if—someone tries to break in.
Your Security, Our Assurance!
Don’t leave your digital assets at risk. Strengthen your defenses now by partnering with Kanerika
What is Data Security?
Data security is the practice of protecting digital information from unauthorized access, corruption, theft, or destruction throughout its entire lifecycle. It encompasses technical safeguards, administrative controls, and physical protections that work together to maintain data confidentiality, integrity, and availability.
The primary goal of data security is to defend against today’s growing spectrum of cyber threats—ransomware, malware, insider threats, social engineering, and human error—while enabling secure and efficient data utilization for business operations.
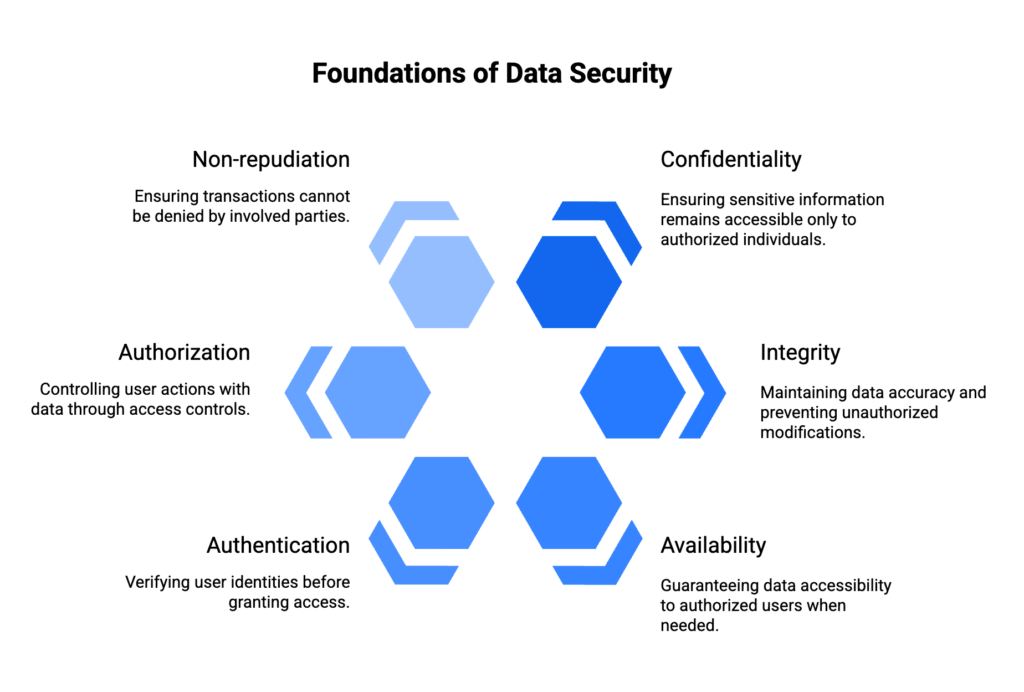
Key Principles of Data Security
- Confidentiality: Ensuring sensitive information remains accessible only to authorized individuals through access controls, encryption, and user authentication mechanisms.
- Integrity: Maintaining data accuracy, completeness, and trustworthiness by preventing unauthorized modifications and detecting any alterations to critical information.
- Availability: Guaranteeing that information systems and data remain accessible to authorized users when needed, even during security incidents or system failures.
- Authentication: Verifying the identity of users, devices, and systems before granting access to sensitive data or resources.
- Authorization: Controlling what authenticated users can do with data, implementing role-based access controls and the principle of least privilege.
- Non-repudiation: Ensuring that data transactions and communications cannot be denied by the parties involved, typically through digital signatures and audit trails.
Data Security vs Data Privacy
While deeply interconnected, data security and data privacy serve distinct but complementary purposes in protecting organizational information.
Data Security Focus Areas
It concentrates on how sensitive information is protected through:
- Firewalls and network security controls
- Data loss prevention (DLP) technologies
- Encryption and tokenization
- Access management systems
- Endpoint protection platforms
- Security monitoring and incident response
Data Privacy Focus Areas
However, data privacy addresses how personal information is collected, processed, stored, and shared:
- Consent management and user rights
- Data minimization and purpose limitation
- Cross-border data transfer regulations
- Individual access and deletion requests
- Privacy impact assessments
- Transparency and disclosure requirements
The Intersection
Privacy regulations like GDPR and CCPA mandate transparency in data usage while granting individuals control over their personal information. Data security measures support these requirements by ensuring only authorized personnel can access personally identifiable information (PII) and that this data is processed securely and compliantly.
In essence, data security protects the data; data privacy governs its use.
For individuals and businesses seeking greater control over their personal data exposure, Incogni offer automated tools to manage and remove personal information from internet.
Why Data Security Matters?
Organizations generate over 402.74 million terabytes of data daily, with the United States alone housing more than 5000 data centers. This massive data volume represents tremendous business value—and equally significant risk exposure.
Direct Financial Impact:
- Average data breach cost: $4.88 million globally
- Healthcare breach cost: $11.05 million average
- Ransomware attack cost: $5.13 million average
- Lost business cost: $1.90 million per breach
Operational Consequences:
- Business disruption and downtime
- Productivity losses during incident response
- System rebuilding and data recovery costs
- Increased cybersecurity insurance premiums
Regulatory Compliance Requirements
The global regulatory landscape continues expanding as data becomes increasingly critical to business operations. Major frameworks include:
- GDPR: Up to 4% of annual global revenue in fines
- CCPA/CPRA: Penalties up to $7,500 per violation
- HIPAA: Fines ranging from $137-$2.067 million
- PCI DSS: Fines up to $500,000 per incident
- SOX: Criminal penalties including imprisonment
In 2024, GDPR enforcement alone resulted in EUR 1.2 billion in fines, demonstrating regulators’ commitment to data protection accountability.
Competitive Advantage and Trust
Robust data security creates measurable business advantages:
- Customer Trust: 86% of consumers care about data privacy and choose businesses with strong security practices
- Partner Confidence: Vendors and partners require security certifications for business relationships
- Market Differentiation: Security leadership becomes a competitive advantage in privacy-conscious markets
- Innovation Enablement: Secure foundations support digital transformation and emerging technology adoption
Types of Data Security Threats
External Cyber Threats
- Ransomware Attacks: Sophisticated encryption-based extortion schemes targeting critical business systems and data. Modern ransomware often includes data exfiltration, threatening public disclosure if ransom demands aren’t met.
- Advanced Persistent Threats (APTs): Long-term, stealthy campaigns targeting specific organizations to steal intellectual property, financial data, or sensitive information over extended periods.
- Phishing and Social Engineering: Manipulating human psychology to trick employees into revealing credentials, installing malware, or providing unauthorized access to systems and data.
- Malware and Virus Attacks: Malicious software designed to infiltrate systems, steal data, disrupt operations, or create backdoors for future attacks.
- Distributed Denial of Service (DDoS): Overwhelming systems with traffic to disrupt availability and potentially mask other malicious activities.
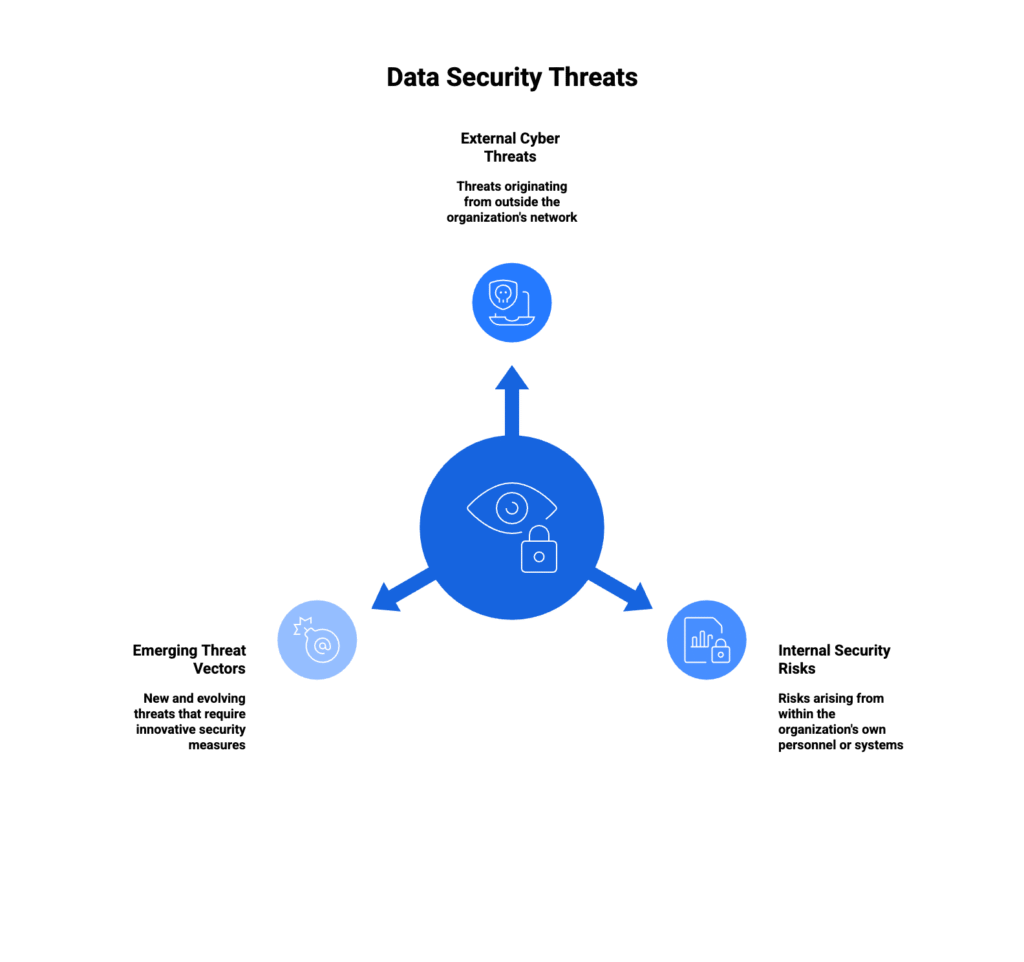
Internal Security Risks
- Insider Threats: Malicious or negligent actions by employees, contractors, or business partners with legitimate access to organizational systems and data.
- Human Error: Accidental data exposure through misconfigured systems, misdirected emails, lost devices, or inadequate security practices.
- Privilege Abuse: Authorized users exceeding their access permissions or using legitimate access for unauthorized purposes.
- Third-Party Vulnerabilities: Security weaknesses in vendor systems, software supply chains, or partner networks that create indirect exposure risks.
Emerging Threat Vectors
- AI-Powered Attacks: Machine learning algorithms used to automate vulnerability discovery, create convincing deepfakes, and enhance social engineering campaigns.
- IoT Device Exploitation: Compromising Internet of Things devices to access networks, steal data, or launch larger attacks against connected infrastructure.
- Cloud Misconfigurations: Improperly configured cloud services exposing sensitive data through inadequate access controls or public storage buckets.
- Supply Chain Attacks: Targeting trusted software vendors or service providers to gain access to their customers’ systems and data.
Data Security Measures and Technologies
Encryption and Data Protection
- Encryption at Rest: Protecting stored data using advanced encryption algorithms like AES-256, ensuring data remains secure even if physical storage devices are compromised or stolen.
- Encryption in Transit: Securing data movement between systems using protocols like TLS 1.3, preventing interception and manipulation during transmission across networks.
- End-to-End Encryption: Providing complete protection from sender to recipient, ensuring only authorized parties possess the decryption keys necessary to access sensitive information.
- Key Management: Implementing centralized key generation, distribution, rotation, and destruction procedures to maintain encryption effectiveness and prevent unauthorized access.
Advanced Authentication Systems
- Multi-Factor Authentication (MFA): Combining multiple verification methods including knowledge factors (passwords), possession factors (tokens), and inherence factors (biometrics) for enhanced security.
- Biometric Authentication: Utilizing unique physical characteristics like fingerprints, facial recognition, iris scanning, and voice patterns for high-security identification and access control.
- Single Sign-On (SSO): Streamlining user access across multiple applications while maintaining centralized authentication and security policy enforcement.
- Privileged Access Management (PAM): Controlling and monitoring administrative access to critical systems through just-in-time access, session recording, and automated credential rotation.
How to Protect Sensitive Data with Microsoft Purview Data Loss Prevention
Microsoft Purview DLP provides robust tools to detect, protect, and manage sensitive information across various platforms such as endpoints, Office 365, OneDrive, SharePoint, Microsoft Teams, and Microsoft 365 Copilot.
Data Protection Technologies
- Data Masking: Obscuring sensitive data elements by replacing them with fictitious yet structurally similar information, enabling development and testing without privacy regulation violations.
- Data Loss Prevention (DLP): Monitoring, detecting, and preventing unauthorized data transfers across email, web, removable media, and cloud applications through content inspection and policy enforcement.
- Secure Data Deletion: Ensuring complete data overwriting and irrecoverability when retiring storage devices or removing sensitive information from systems.
- Data Tokenization: Replacing sensitive data with unique identification symbols while maintaining data utility for processing without exposing actual values.
Top Data Security Tools
Securing business data isn’t only about blocking hackers—it’s also about controlling access, ensuring compliance, and managing information responsibly. Several enterprise tools stand out in this space:
1. Databricks
Databricks offers a secure platform for managing and analyzing large volumes of data. With features like role-based access control and audit logging, it helps organizations protect sensitive information while still enabling teams to collaborate.

2. Collibra
Collibra is widely used for data governance. It ensures that only the right people have access to the right data. By creating a clear framework for data ownership, quality, and compliance, Collibra reduces the risk of accidental leaks or misuse.
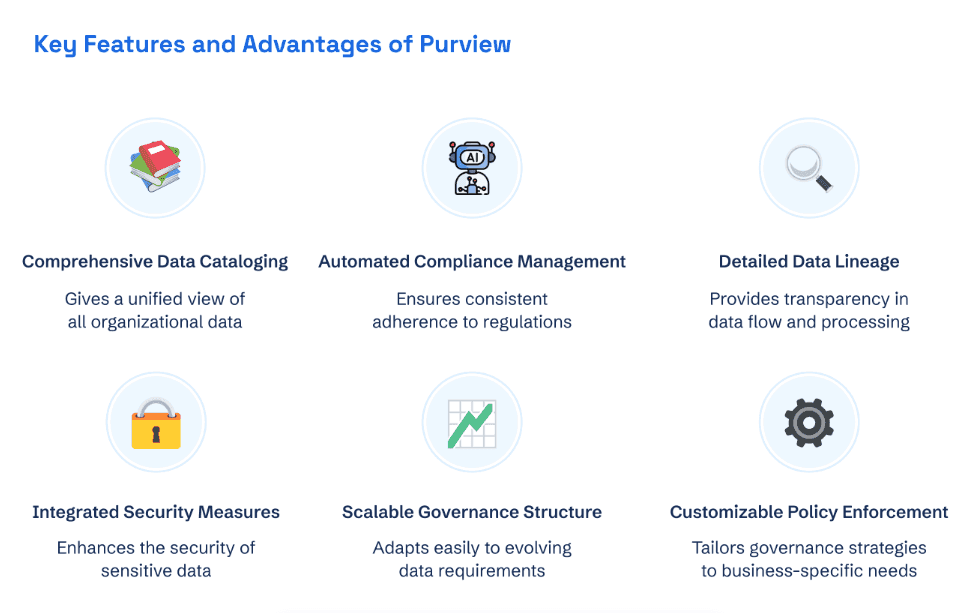
3. Microsoft Purview
Purview provides unified data governance across on-premises, cloud, and SaaS platforms. Its strong classification, lineage tracking, and regulatory compliance tools help businesses keep data secure while meeting privacy requirements.
4. Informatica
Informatica combines data integration with governance and security controls. It provides encryption, masking, and monitoring to safeguard sensitive assets across systems.
Together, these tools give businesses visibility, control, and protection. Instead of treating security as an add-on, they embed it directly into how data is stored, shared, and used.
Data Security and Compliance
Global Regulatory Landscape
The regulatory environment continues evolving as data becomes more critical to business operations and more valuable to cybercriminals:
- General Data Protection Regulation (GDPR): European Union’s comprehensive privacy law affecting any organization processing EU citizens’ personal data, with fines up to 4% of annual global revenue or €20 million, whichever is higher.
- California Consumer Privacy Act (CCPA) / California Privacy Rights Act (CPRA): Provides California residents with enhanced privacy rights including data access, deletion, and opt-out of sale, with penalties up to $7,500 per intentional violation.
- Health Insurance Portability and Accountability Act (HIPAA): Protects patient health information in healthcare organizations through detailed security and privacy requirements, with fines ranging from $137 to $2.067 million.
- Payment Card Industry Data Security Standard (PCI DSS): Mandates specific security measures for organizations handling credit card information, with non-compliance fines up to $500,000 per incident.
- Sarbanes-Oxley Act (SOX): Requires public companies to maintain accurate financial records and implement internal controls, with criminal penalties including imprisonment for executives.
Emerging Global Regulations
- Digital Personal Data Protection Act (India): India’s comprehensive privacy law affecting organizations processing Indian citizens’ personal data.
- Personal Information Protection Law (PIPL) (China): China’s data protection regulation governing personal information processing with significant extraterritorial reach.
- Lei Geral de Proteção de Dados (LGPD) (Brazil): Brazil’s general data protection law modeled after GDPR with similar requirements and penalties.
Data Analytics in the Automotive Industry: How Top Brands Stay Ahead
From virtual assistants to generative design, data analytics in the automotive industry is enabling companies to blend innovation with comfort and safety.
Compliance Implementation Strategy
- Gap Analysis: Systematic evaluation of current practices against regulatory requirements to identify areas needing improvement or additional controls.
- Documentation Requirements: Maintaining comprehensive records of data processing activities, security measures, breach notifications, and compliance demonstrations.
- Regular Audits: Internal and external assessments to validate ongoing compliance and identify potential violations before regulatory examinations.
- Cross-Border Data Transfers: Implementing appropriate safeguards for international data movements including adequacy decisions, standard contractual clauses, and binding corporate rules.
Network and Endpoint Security
- Next-Generation Firewalls: Advanced network protection combining traditional firewall capabilities with application awareness, intrusion prevention, and advanced threat detection.
- Endpoint Detection and Response (EDR): Continuous monitoring and analysis of endpoint activities to detect and respond to suspicious behaviors and potential security incidents.
- Network Segmentation: Isolating critical systems and data through micro-segmentation, limiting lateral movement during security breaches and containing potential damage.
- Intrusion Detection and Prevention Systems (IDS/IPS): Real-time monitoring of network traffic and system activities to identify and block malicious activities automatically.
Kanerika: Your Ideal Data Security Partner
Why Choose Kanerika for Data Security
When it comes to keeping your data safe and well-governed, Kanerika brings clarity, structure, and compliance front and center. Three core offerings—KanGovern, KANComply, and KanSecure—work together to give you peace of mind:
- KanGovern lays the groundwork for smart data governance. It helps you discover, catalog, and manage your data assets efficiently, cutting through silos and giving your team visibility and control.
- KanComply ensures your operations line up with global laws and industry rules. With support for over 360 international regulations, it guides you in managing compliance head‑on, not as an afterthought.
- KanGuard focuses on securing your data with enforcement, policy-driven protection, and risk monitoring. It builds a safe environment where only the right people and systems can access sensitive data.
By combining those three, Kanerika doesn’t just protect your data—it makes managing, understanding, and complying with it simpler, smarter, and more measurable. That kind of setup pays off: fewer risks, clearer policies, and stronger confidence for your team—and your leadership.
Case Study: Kanerika’s Microsoft Purview Implementation
Kanerika successfully implemented Microsoft Purview for a leading enterprise client, delivering measurable improvements in data governance, security, and operational efficiency. This isn’t theory — it’s execution.
Client Challenge:
The organization struggled with fragmented data tools, manual classification processes, and siloed environments that compromised compliance and collaboration.
Kanerika’s Solution:
Leveraging Microsoft Purview, Kanerika deployed:
- Automated data discovery using Purview’s Data Map
- Sensitive data classification with improved visibility and control
- End-to-end data lineage from source systems to analytics in the Lakehouse
Outcome Delivered:
- 30% boost in reporting efficiency
- 25% reduction in audit time
- 90% increase in informed decision-making
Your Security, Our Assurance!
Don’t leave your digital assets at risk. Strengthen your defenses now by partnering with Kanerika
FAQs
What do you mean by data security?
Data security refers to the protective measures, policies, and technologies that safeguard digital information from unauthorized access, corruption, or theft throughout its lifecycle. This encompasses encryption protocols, access controls, network security, and physical safeguards that collectively prevent data breaches and ensure information integrity. Effective data security strategies address both internal threats and external cyberattacks while maintaining compliance with industry regulations. Organizations implement layered security frameworks to protect sensitive business and customer data across storage, transmission, and processing environments. Kanerika delivers enterprise-grade data security solutions built for compliance and trust—connect with our team to strengthen your security posture.
Why do we need data security?
Data security is essential because cyber threats continue escalating while regulatory penalties for breaches grow more severe. Organizations store vast amounts of sensitive customer information, intellectual property, and financial records that attackers actively target. Without robust data security measures, businesses face operational disruptions, reputational damage, legal consequences, and significant financial losses from ransomware attacks or data theft. Protecting information assets also builds customer trust and ensures business continuity during incidents. Compliance frameworks like GDPR and HIPAA mandate specific security controls, making protection a legal requirement. Kanerika helps enterprises implement comprehensive data governance and security frameworks—schedule a consultation to assess your vulnerabilities.
What are 5 ways to secure data?
Five proven ways to secure data include implementing end-to-end encryption for data at rest and in transit, deploying multi-factor authentication across all access points, establishing role-based access controls to limit data exposure, conducting regular security audits and vulnerability assessments, and maintaining comprehensive backup and disaster recovery protocols. These data protection methods work together to create defense-in-depth, ensuring no single point of failure compromises your information assets. Organizations should also train employees on security awareness to reduce human error risks. Kanerika’s data security specialists design tailored protection strategies aligned with your infrastructure—reach out for a free security assessment.
What are the 5 pillars of data security?
The five pillars of data security are confidentiality, integrity, availability, authentication, and non-repudiation. Confidentiality ensures only authorized users access sensitive information through encryption and access controls. Integrity guarantees data remains unaltered and accurate during storage and transmission. Availability maintains consistent access to systems and information when needed. Authentication verifies user identities before granting access. Non-repudiation provides proof of data origin and delivery, preventing denial of actions. Together, these pillars form a comprehensive data security framework that addresses threats from multiple angles. Kanerika builds security architectures anchored in these principles—talk to our experts about fortifying your data environment.
What are the benefits of data security?
Strong data security delivers multiple business benefits including protection against costly data breaches, regulatory compliance with standards like GDPR and HIPAA, and enhanced customer trust through demonstrated commitment to privacy. Organizations gain competitive advantage by safeguarding intellectual property and trade secrets from corporate espionage. Effective security measures reduce downtime from cyberattacks, maintaining operational continuity and revenue streams. Additionally, robust data protection supports digital transformation initiatives by enabling secure cloud adoption and data sharing across partners. Insurance premiums often decrease when companies demonstrate mature security postures. Kanerika’s security and governance solutions help enterprises unlock these benefits—contact us to explore your options.
What are the 3 types of data security?
The three primary types of data security are administrative, physical, and technical controls. Administrative security encompasses policies, procedures, and employee training programs that govern how organizations handle sensitive information. Physical security protects hardware, facilities, and storage media through measures like biometric access, surveillance systems, and secure data centers. Technical security includes software-based protections such as encryption, firewalls, intrusion detection systems, and access management tools. Effective data security programs integrate all three types into a cohesive strategy that addresses vulnerabilities across people, processes, and technology layers. Kanerika implements holistic security frameworks covering all control types—schedule a discovery call to evaluate your current state.
Who is responsible for data security?
Data security responsibility spans the entire organization, from executives to individual employees. The Chief Information Security Officer leads strategy and policy development, while IT teams implement technical controls and monitor threats. Data owners within business units classify information and define access requirements. Legal and compliance teams ensure regulatory adherence. However, every employee shares accountability through secure practices like strong password hygiene, phishing awareness, and proper data handling. Board-level oversight increasingly drives security investment and risk management decisions. This shared responsibility model creates security-conscious culture throughout the enterprise. Kanerika partners with organizations to establish clear data governance roles and accountability frameworks—let us help define your security responsibilities.
What are the four elements of data security?
The four core elements of data security are protection, detection, response, and recovery. Protection involves preventive measures like encryption, access controls, and firewalls that block unauthorized access. Detection encompasses monitoring tools, intrusion detection systems, and security analytics that identify threats and anomalies in real-time. Response includes incident management procedures, threat containment protocols, and communication plans activated when breaches occur. Recovery focuses on backup restoration, system rebuilding, and business continuity measures that restore operations after incidents. These elements form a continuous cycle that strengthens security posture over time through lessons learned. Kanerika designs data security architectures addressing all four elements—connect with us to build your comprehensive defense strategy.
What are the 3 principles of data security?
The three foundational principles of data security are confidentiality, integrity, and availability, collectively known as the CIA triad. Confidentiality ensures sensitive information remains accessible only to authorized individuals through encryption and access management. Integrity maintains data accuracy and consistency by preventing unauthorized modifications through checksums, digital signatures, and audit trails. Availability guarantees reliable access to information and systems when needed through redundancy, failover mechanisms, and disaster recovery planning. Every security control, policy, and technology should support at least one of these principles. Balancing all three creates resilient data protection that meets business needs. Kanerika implements security solutions built on CIA triad principles—reach out to strengthen your data protection foundation.
Which is the most secure way to protect data?
The most secure way to protect data combines multiple layers of defense rather than relying on any single method. End-to-end encryption using AES-256 provides the strongest protection for data at rest and in transit, making intercepted information unreadable without proper keys. However, encryption alone falls short without complementary measures including zero-trust architecture, multi-factor authentication, network segmentation, and continuous monitoring. Hardware security modules offer additional protection for encryption keys themselves. Regular penetration testing validates that controls work as intended. Defense-in-depth ensures that if one layer fails, others continue protecting sensitive information. Kanerika architects multi-layered data security solutions tailored to enterprise requirements—start with a security assessment to identify your optimal protection strategy.
What do you mean by data protection and security?
Data protection and security are related but distinct concepts that work together to safeguard information assets. Data security focuses on defending against unauthorized access, cyberattacks, and breaches through technical controls like encryption, firewalls, and access management. Data protection encompasses broader practices including privacy compliance, backup and recovery procedures, data lifecycle management, and individual rights under regulations like GDPR. While security prevents malicious actors from accessing data, protection ensures proper handling, storage, and disposal throughout information’s lifecycle. Organizations need both disciplines to maintain regulatory compliance and build customer trust. Kanerika delivers integrated data protection and security solutions built for compliance—contact our team to unify your approach.
What do you mean by data security measures?
Data security measures are the specific controls, technologies, and procedures organizations implement to protect information from unauthorized access, theft, or corruption. These measures span technical solutions like encryption algorithms, firewalls, intrusion prevention systems, and endpoint protection software. Administrative measures include security policies, employee training programs, incident response plans, and access review processes. Physical measures encompass secured facilities, surveillance systems, and hardware disposal protocols. Effective data security measures align with risk assessments, addressing the most critical vulnerabilities while meeting compliance requirements. Organizations should regularly evaluate and update measures as threats evolve and business needs change. Kanerika helps enterprises implement comprehensive data security measures across all control categories—request a consultation to optimize your security investments.
What are the three data security measures?
Three essential data security measures every organization should implement are encryption, access control, and data backup. Encryption transforms readable data into coded formats that only authorized parties with decryption keys can access, protecting information during storage and transmission. Access control restricts data availability based on user roles, authentication credentials, and business need, following least-privilege principles. Data backup creates recoverable copies stored in separate locations, ensuring business continuity after ransomware attacks, hardware failures, or disasters. These foundational measures address core security requirements across confidentiality, integrity, and availability. Together they form the baseline for any data protection strategy. Kanerika implements these critical security measures with enterprise-grade tools and governance—speak with our specialists about securing your data environment.
What is the 3-2-1 rule for data protection?
The 3-2-1 rule for data protection is a backup strategy requiring three copies of data stored on two different media types with one copy kept offsite. This approach ensures redundancy protects against hardware failures, ransomware encryption, natural disasters, and site-specific incidents. For example, maintain production data, a local backup on separate storage, and a cloud-based or geographically distant copy. Modern variations include 3-2-1-1 adding an immutable copy, or 3-2-1-1-0 requiring verified backups with zero errors. Following this data backup best practice significantly improves recovery success rates and reduces downtime after incidents. Kanerika designs resilient backup and disaster recovery architectures following proven protection standards—let us build your data protection strategy.
What are the 5 components of data security?
The five key components of data security are identification, authentication, authorization, encryption, and auditing. Identification establishes user identity through usernames or certificates. Authentication verifies identity claims using passwords, biometrics, or multi-factor methods. Authorization determines access permissions based on roles and policies after authentication succeeds. Encryption protects data confidentiality by converting information into unreadable formats without proper keys. Auditing maintains detailed logs of access attempts, changes, and security events for compliance and forensic analysis. These components work together within a comprehensive data security framework, each addressing specific protection requirements. Weakness in any component creates vulnerability exploitable by attackers. Kanerika integrates all five components into cohesive enterprise security solutions—connect with our team for a comprehensive security review.
What is another name for data security?
Data security is also referred to as information security, cybersecurity, or data protection depending on context and scope. Information security broadly covers protecting all forms of information including digital and physical assets. Cybersecurity specifically addresses digital threats and network-based attacks. Data protection often emphasizes privacy compliance and personal information handling under regulations like GDPR. Additional related terms include computer security, IT security, and information assurance. While these terms overlap significantly, subtle distinctions exist in their focus areas. Organizations may use these terms interchangeably, though data security specifically centers on safeguarding structured and unstructured data assets from unauthorized access. Kanerika provides comprehensive information security services covering all aspects of data protection—explore how we can secure your enterprise data.
What are the 5 importance of data security?
Five critical importance factors of data security include protecting sensitive business and customer information from theft, ensuring compliance with regulations like GDPR, HIPAA, and SOC 2 to avoid penalties, maintaining customer trust and brand reputation in competitive markets, enabling secure digital transformation and cloud adoption initiatives, and ensuring business continuity by preventing costly downtime from cyberattacks. Organizations that prioritize data security also gain competitive advantages through demonstrated commitment to protecting stakeholder information. Additionally, strong security postures attract enterprise customers with strict vendor requirements and reduce insurance premiums. These factors make data security investment essential for sustainable business operations. Kanerika helps enterprises realize the full value of robust data security—schedule a consultation to discuss your security priorities.
What are the three types of data protection?
The three types of data protection are traditional backup and recovery, data security controls, and privacy compliance measures. Backup and recovery ensures data availability through regular copies, replication, and disaster recovery procedures that restore operations after incidents. Security controls protect data confidentiality and integrity through encryption, access management, and threat prevention technologies. Privacy compliance addresses regulatory requirements governing personal data collection, processing, storage, and individual rights under laws like GDPR and CCPA. Organizations need all three types working together to comprehensively protect information assets while meeting legal obligations and business continuity requirements. Kanerika delivers integrated data protection strategies covering backup, security, and compliance—contact us to build your unified protection framework.









