When NVIDIA CEO Jensen Huang called OpenClaw “probably the single most important release of software, probably ever” at the Morgan Stanley TMT Conference in March 2026, the AI agent space took notice. OpenClaw went from a weekend project to 250,000+ GitHub stars in under four months, making it the fastest-growing open-source project in GitHub history. But viral growth and production readiness are two different things, and the gap between them is exactly why developers are searching for OpenClaw alternatives.
The tool’s core problem is access. OpenClaw runs with unrestricted permissions on your machine from the moment you install it. Security researchers at Palo Alto Networks have flagged it publicly, Cisco’s team found data exfiltration in third-party skills, and even one of OpenClaw’s own maintainers warned that the project is “far too dangerous” for anyone who cannot fully audit what they are running. China moved to restrict it across state agencies and enterprises in March 2026 for exactly these reasons.
This blog covers the best OpenClaw alternatives available in 2026, across seven tools, compared on security model, system requirements, ease of setup, and use case fit. Whether you are a developer looking for a lightweight replacement, a team with compliance requirements, or someone who just wants an agent that does not run with god-mode permissions by default, there is a practical option here for you.
Key Takeaways
- OpenClaw’s core risk is unrestricted system access by default, not missing features.
- NanoClaw sandboxes every action in containers; NemoClaw adds enterprise-grade policy controls on top.
- Nanobot’s entire 4,000-line codebase can be audited in hours. OpenClaw’s 430,000 lines cannot.
- PicoClaw runs on under 10MB RAM, making it the only viable pick for minimal hardware setups.
- Choosing an agent without container isolation or governance is a documented security risk, not just a preference call.
Why Is Everyone Looking for an OpenClaw Alternative?
OpenClaw is an open-source personal AI agent framework built by PSPDFKit founder Peter Steinberger. It connects large language models like Claude, GPT-4, and Llama to messaging apps such as WhatsApp, Telegram, and Discord, letting users issue chat commands that trigger real actions on their local machine. By early 2026, it had crossed 260,000 GitHub stars and become the fastest-growing open-source project in GitHub history.
That growth came with problems teams building for production quickly ran into.
1. Over-permissions by Default
OpenClaw runs with admin-level system access out of the box. There is no sandboxing unless you configure it yourself. Security researchers from Palo Alto Networks described it as a “lethal trifecta”: access to private data, exposure to untrusted content, and outbound external communication. By March 2026, researchers had identified 8 critical CVEs, including one enabling one-click remote code execution.
2. Unpredictable Execution
OpenClaw lets the AI decide its next action probabilistically, so execution paths vary between runs. There is no enforced state machine. Engineers building repeatable workflows report this non-determinism as a consistent blocker in anything beyond personal experimentation.
3. Not Stable for Production
The codebase spans 430,000+ lines of TypeScript, making it hard to audit. The ClawHub skill registry was found to contain roughly 900 malicious skills by early 2026, accounting for about 20% of the registry. The project’s own FAQ states there is no perfectly secure setup.
Build Smarter with Kanerika’s AI Solutions!
Partner with Kanerika for Expert AI implementation Services
Limitations of OpenClaw
OpenClaw earned its reputation fast, but production use has exposed real limitations that go beyond setup friction. The security concerns are documented, the codebase is difficult to audit, and the default “full system trust” model is a hard sell for teams with any compliance requirements.
1. Security exposure
OpenClaw runs with broad system access by default. Researchers discovered CVE-2026-25253, which allows remote code execution, and CVE-2026-26327, an authentication bypass. A supply chain attack called ClawHavoc compromised over 9,000 installations through malicious skills in the plugin registry.
2. Lack of OS-level isolation
The security model operates at the application layer through allowlists and pairing codes. There is no containerization by default, so a compromised agent can access SSH keys, cloud credentials, and sensitive files on the host machine.
3. Complexity and resource weight
OpenClaw runs nearly 430,000 lines of code with 70+ dependencies. It requires Node.js, at minimum 16GB RAM, and a dedicated machine to run reliably. Setup involves terminal commands and manual API key configuration.
4. Unpredictable automation
Because the agent runs persistently with broad permissions, edge cases can produce unintended actions. One widely reported incident involved an agent creating a dating profile without explicit user direction.
5. Plugin ecosystem risks
The ClawHub skill registry lacks adequate vetting. Researchers found malicious payloads in third-party skills designed to exfiltrate credentials and inject malicious instructions.
The response from the developer community has been rapid. A wave of alternatives emerged within weeks of OpenClaw going viral, each addressing a specific weakness: lighter resource requirements, better isolation, simpler codebases, or stronger defaults.
Top 7 OpenClaw Alternatives in 2026
The tools below cover the main use cases that have emerged since OpenClaw went mainstream. Some are direct spiritual successors. Others existed before OpenClaw but have gained visibility as teams look for production-ready alternatives.
| Tool | Best For | Type | Key Strength |
| NanoClaw | Security-conscious users | Lightweight agent | OS-level container isolation |
| Nanobot | Researchers and automation builders | Lightweight agent (Python) | 99% smaller codebase, easy to audit |
| PicoClaw | Edge and low-resource setups | Lightweight agent (Go) | Runs on under 10MB RAM, sub-1s boot |
| TrustClaw | Cloud-hosted, compliance-focused users | Cloud AI agent | OAuth auth + sandboxed execution |
| memU | Users who want persistent context | Personal AI Agent | Long-term knowledge graph memory |
| SuperAGI | Developers building multi-agent systems | Open-source framework | Multi-agent orchestration and customization |
| ZeroClaw | Performance-critical and edge deployments | Lightweight agent (Rust) | 3.4MB binary, sub-10ms startup |
Detailed Breakdown of Each OpenClaw Alternative
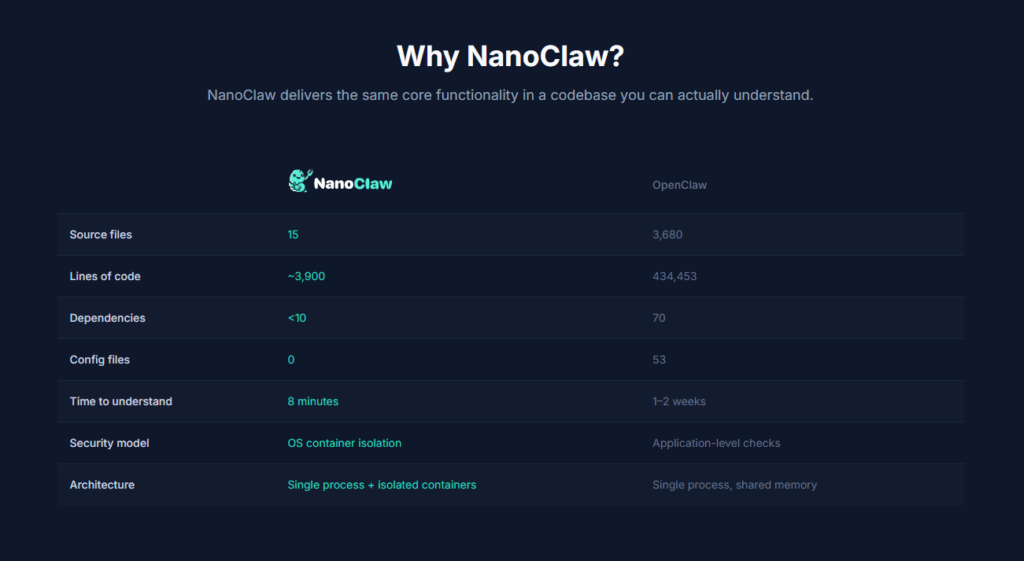
1. NanoClaw
NanoClaw was built as a direct response to OpenClaw’s security problems. Its core is around 500 lines of TypeScript, and every agent runs inside an isolated Docker container or macOS Apple Container. It connects to WhatsApp, Telegram, Discord, Slack, and Gmail, with each channel getting its own sandboxed context and memory. It runs on the Claude Agent SDK, meaning Claude Code handles the reasoning and can modify the codebase itself on request.
Pros: Strongest security model of any personal agent on this list; codebase is small enough to audit in full; container isolation is the default, not an optional configuration.
Cons: Claude-only, no multi-LLM support; minimal plugin ecosystem; requires comfort with Docker or Apple Container to deploy correctly.
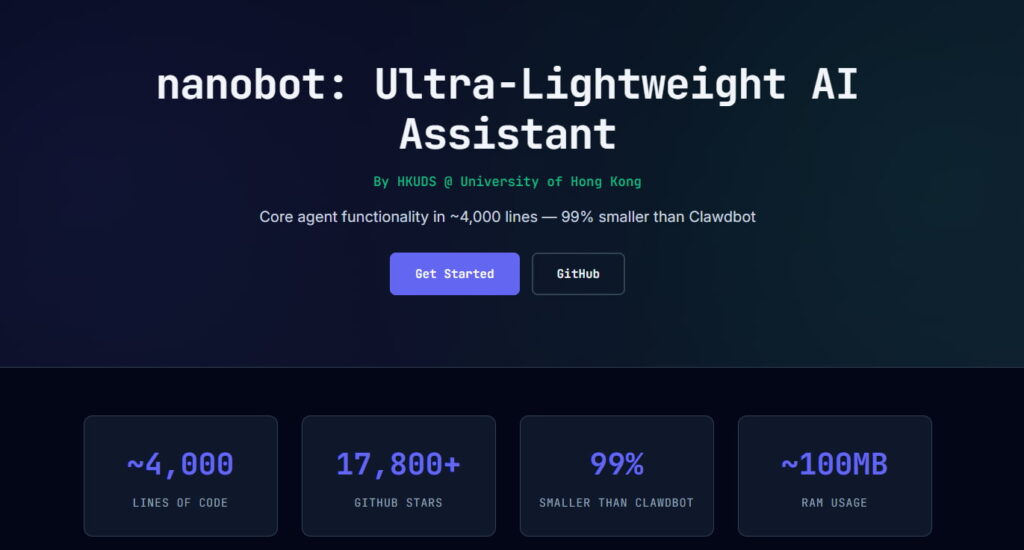
2. Nanobot
Nanobot delivers OpenClaw’s core agent functionality in just 4,000 lines of Python, developed by the Data Intelligence Lab at the University of Hong Kong. The entire codebase can be read in a few hours, which is the point. It supports persistent memory across sessions, integrated web search, and multi-provider LLM support including OpenAI, Anthropic, and local models via Ollama. Development is active, with near-daily releases through early 2026.
Pros: Fully readable and auditable codebase; fast setup; multi-LLM support including local models; strong learning resource for developers who want to understand agent architecture.
Cons: Minimal UI, mostly config files and console logs; connects to only a couple of messaging platforms out of the box; no plugin marketplace; too bare-bones for production enterprise workflows.
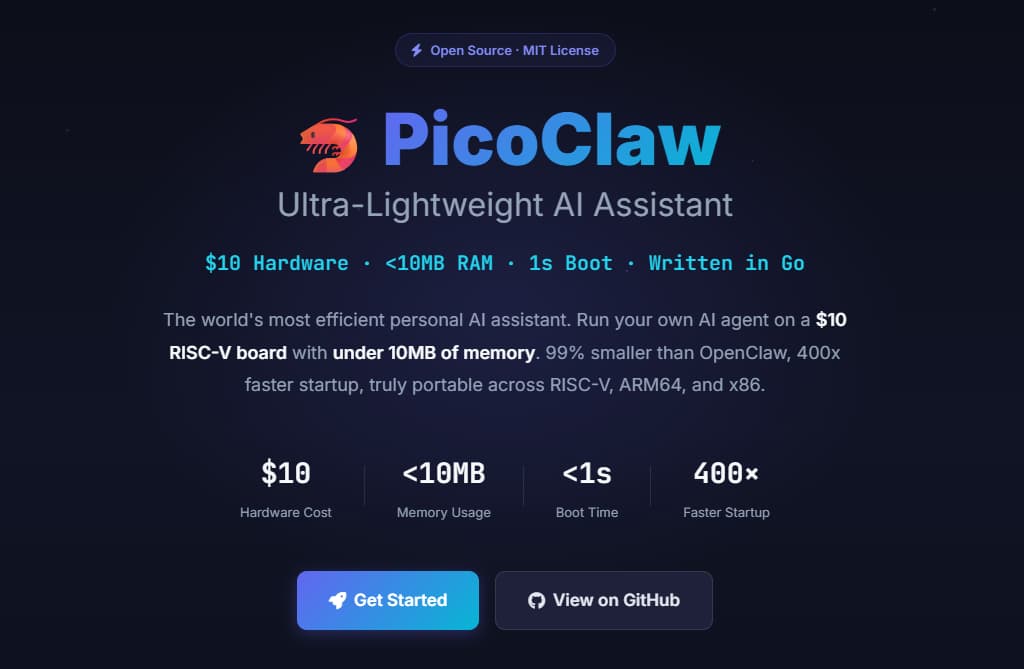
3. PicoClaw
PicoClaw is an independent open-source project by Sipeed, written entirely in Go. It is not a fork of OpenClaw or Nanobot but was rebuilt from scratch through a self-bootstrapping process where the AI agent itself drove the architectural migration. The headline capability is resource efficiency: it runs on under 10MB RAM on $10 hardware, making it the only tool in this comparison built for genuinely minimal or edge computing setups.
Pros: Runs on hardware every other tool on this list cannot; Go-based architecture makes it fast and portable; clean codebase with minimal dependencies.
Cons: Early-stage ecosystem with fewer integrations; smaller community compared to NanoClaw or Nanobot; limited documentation for non-standard deployments.
4. NemoClaw
NemoClaw is NVIDIA’s open-source security stack built on top of OpenClaw, released in March 2026. It adds three layers: OpenShell for kernel-level sandboxing of every agent action, a YAML-based policy engine that defines exactly what each agent can access and call, and a privacy router that keeps sensitive data on local models while routing general tasks to cloud providers. It is the only tool here backed by a major infrastructure company with formal enterprise partnerships.
Pros: The strongest governance layer available for OpenClaw-style agents; policy-based access controls per agent; audit logging and rollback; backed by NVIDIA with enterprise partnerships already in place.
Cons: Pricing not yet announced but expected to reflect enterprise positioning; YAML policy configuration requires significant setup time from security teams; still in early preview as of March 2026.
5. memU
memU takes a different angle from every other tool on this list. Rather than focusing on raw task execution, it builds a local knowledge graph of your preferences, projects, and habits over time. The memory is hierarchical, not flat, which means the agent understands relationships between information rather than just storing conversation logs. It also acts proactively based on behavior patterns without waiting for explicit commands, and compresses context before API calls to keep costs down.
Pros: Best long-term memory architecture of any personal agent; proactive behavior without explicit prompting; token optimization reduces ongoing API costs.
Cons: Not built for raw execution tasks like shell commands or code generation; performance tied to local hardware for memory retrieval; less suitable for developer-heavy or automation-first workflows.

6. SuperAGI
SuperAGI is an open-source framework for building autonomous AI agents that can plan, reason, and act across complex multi-step workflows. The distinction from other tools here is that it is not a finished product you deploy and use — it is a foundation you build on. It supports multiple agents running in parallel on separate tasks, long-term memory storage, and a plugin architecture that the community actively extends. It is used heavily in research environments and by teams building custom, internal AI-driven processes.
Pros: Most flexible and customizable option on this list; strong multi-agent support; robust memory system for long-running tasks; active open-source community with shared plugins.
Cons: No polished UI or setup wizard; requires significant engineering effort to configure and maintain; not suitable for non-technical teams; community support only, no formal vendor backing.
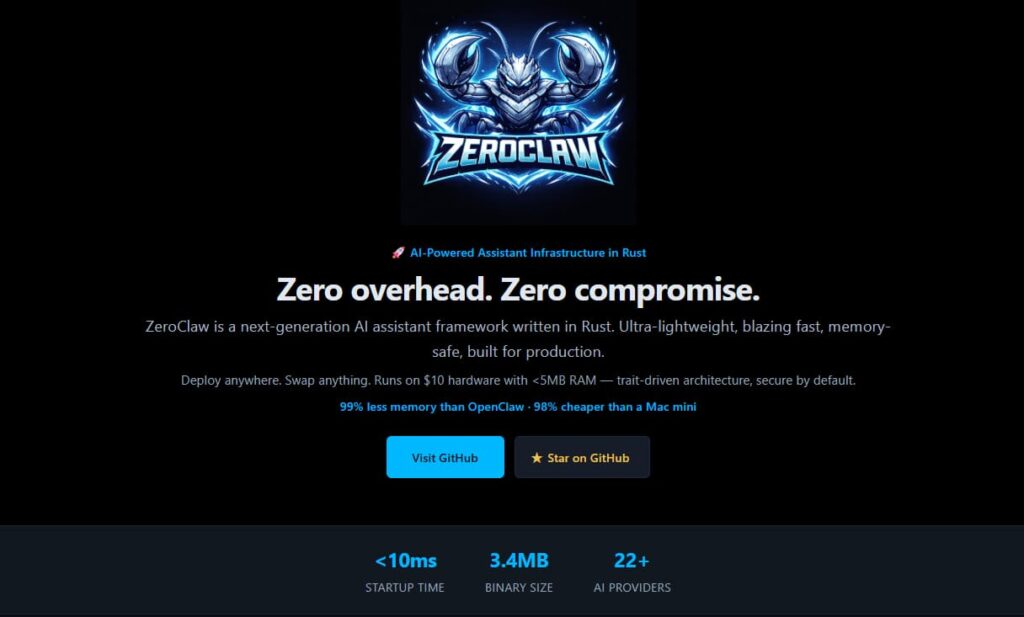
7. ZeroClaw
ZeroClaw sits at the minimal end of the Claw-family ecosystem. It is built for users who want controlled, scoped agent execution without the complexity or attack surface that comes with a larger tool. The codebase is small, the permissions are limited by default, and the setup is straightforward for developers comfortable with the terminal. It works well as a lightweight local agent for simple, repeatable tasks where predictability matters more than feature depth.
Pros: Simple to audit and deploy; limited default permissions reduce risk; low resource footprint; clean execution model for well-defined workflows.
Cons: Limited integrations and a smaller development community; not suited for complex multi-step or multi-agent workflows; fewer resources and documentation compared to more established tools on this list.
Which OpenClaw Alternative Is Best for Your Use Case?
The right choice depends more on your constraints than on feature lists. Here is how to match each tool to a specific situation.
- Developers building multi-agent systems: SuperAGI. It is the only framework here built specifically for orchestrating specialized agents working in parallel. You will need to configure it, but it gives you full control over reasoning logic, memory, and tool access.
- Low-resource or edge environments: ZeroClaw or PicoClaw. ZeroClaw’s Rust binary runs on commodity hardware with almost no footprint. PicoClaw goes further, running on $10 microcontrollers with under 10MB RAM. Both work offline with local models.
- Automation workflows: Nanobot. The Python codebase makes it fast to extend and customize for specific automation tasks. The minimal footprint also means lower operational costs when running scheduled jobs.
- Security-first or regulated industries: NanoClaw or TrustClaw. NanoClaw gives you open-source transparency plus container isolation. TrustClaw gives you managed cloud hosting with OAuth and sandboxing if you prefer not to run infrastructure yourself.
- Beginners and general users: PicoClaw or memU. PicoClaw’s single-binary setup keeps things simple. memU requires minimal configuration and gets more useful over time without requiring any technical customization.
| Use Case | Best Tool | Reason |
| Multi-agent development | SuperAGI | Parallel agents, custom orchestration |
| Low RAM / edge hardware | ZeroClaw / PicoClaw | Sub-10MB footprint, offline capable |
| Automation workflows | Nanobot | Python-native, fast to extend |
| Security and compliance | NanoClaw / TrustClaw | Container isolation or cloud sandboxing |
| Beginners / general use | PicoClaw / memU | Simple setup, low maintenance |
Are These OpenClaw Alternatives Safer and More Reliable?
Safety in this context comes down to three things: what the agent can access by default, what happens if it behaves unexpectedly, and how well the codebase can be audited for vulnerabilities.
OpenClaw runs with host-level permissions and no default containment. A misconfigured agent or a malicious third-party skill has full access to your file system, credentials, and network. That is not a fringe concern. Security researchers documented multiple CVEs and a large-scale supply chain attack within the first two months of the project going viral.
The alternatives take meaningfully different approaches:
- NanoClaw provides the strongest isolation model of any personal agent. Container-per-session means agent actions are physically restricted to a sandbox. Even the Dextralabs SARA security assessment rates it highest for compliance alignment among comparable frameworks.
- ZeroClaw defaults to a restrictive execution environment. Capabilities are explicitly granted rather than broadly given. This is safer by default even if the isolation is not as complete as NanoClaw’s containers.
- Lightweight tools (PicoClaw, Nanobot) are safer primarily through simplicity. Smaller codebases mean fewer attack vectors. But they lack formal security models, so they are not appropriate for environments handling sensitive or regulated data without additional hardening.
- TrustClaw removes the local execution problem entirely by hosting the agent in a managed environment with sandboxing built in. For teams that do not want to manage security infrastructure themselves, this is a practical choice.
- SuperAGI is powerful but complex. Security is better than OpenClaw for teams that configure it correctly, but the setup surface area is large and misconfiguration is a real risk for teams without DevOps depth.
None of these alternatives are zero-risk. Any agent with tool access can produce unintended actions. The question is whether the blast radius of a mistake is limited to a container or extends to your entire host machine.
Kanerika’s AI Approach: From Raw Data to Business Intelligence
Kanerika helps enterprises turn complex data into decisions that actually move the business forward. Built on Microsoft technologies including Power BI, Azure ML, and Microsoft Fabric, Kanerika’s solutions bring together interactive dashboards, predictive analytics, and automated reporting to support faster, more confident decision-making across healthcare, finance, retail, and logistics.
The capability set spans AI strategy, predictive modeling, intelligent automation, marketing workflow optimization, data engineering, and low-code development. Organizations work with Kanerika to forecast trends, understand customer behavior, streamline operations, and manage cloud and hybrid environments with the governance practices that regulated industries require. ISO 9001, ISO 27001, and ISO 27701 certifications reflect how seriously security and privacy are treated across every engagement.
Kanerika’s enterprise AI agents, including DokGPT, Jennifer, Alan, Susan, KARL, Mike, and Jarvis, are built for document intelligence, risk assessment, customer insights, and voice analytics. Each agent is designed for scalability, trained on structured enterprise data, and built to integrate into existing systems without requiring a rebuild of the underlying infrastructure.
Transform Your Business with AI-Powered Solutions!
Partner with Kanerika for Expert AI implementation Services
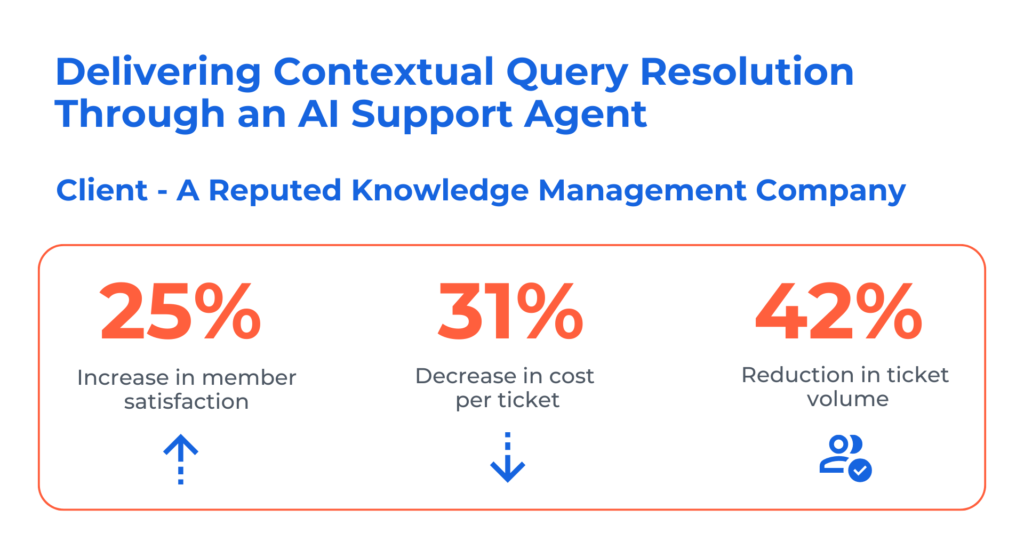
Case Study: Delivering Contextual Query Resolutions for a Knowledge Management Firm
The client is a global leader in facilitating knowledge-sharing between industry experts and decision-makers. With access to a network of over one million subject-matter experts, the organization connects professionals to real-world insights through consultations, surveys, and on-demand expertise. Their mission is to help clients make smarter, faster decisions by bridging the gap between complex questions and expert perspectives across industries and domains.
Client’s Challenges:
- High volume of repetitive tickets tied up skilled executives in routine resolutions.
- Manual lookup across a siloed knowledge base and historical ticket archive slowed responses.
- Extended TATs frustrated network members, impacting satisfaction.
- Escalations to executives for straightforward queries drove up support costs.
Solutions:
Kanerika developed an AI-powered support agent that integrates seamlessly with:
- The centralized knowledge base of guidelines and FAQs
- The organization’s Zendesk instance for historic ticket retrieval
- Chat and voice channels for member engagement
Results:
- 65% self-service resolution rate
- 42% reduction in ticket volume
- 31% decrease in cost per ticket
FAQs
Is there a safer alternative to OpenClaw?
Enterprise-grade agentic AI platforms offer significantly safer alternatives to OpenClaw by providing built-in governance, security controls, and compliance frameworks. These platforms include PII redaction capabilities, role-based access controls, and audit trails that OpenClaw lacks natively. Organizations handling sensitive data benefit from solutions with SOC 2 compliance and enterprise-level encryption. The key differentiator is purpose-built security architecture rather than bolted-on protections. Kanerika’s AI Workforce platform delivers autonomous agents with compliance-first design—connect with our team to evaluate a secure OpenClaw replacement for your environment.
What replaced OpenClaw?
Enterprise agentic AI platforms have emerged as OpenClaw replacements, offering production-ready autonomous agents with built-in governance and security. Organizations migrating from OpenClaw typically move toward unified platforms that combine agent orchestration with data quality controls and compliance features. Solutions featuring autonomous AI agents for specific business functions—legal document processing, data analysis, and workflow automation—now dominate enterprise deployments. The shift prioritizes reliability, scalability, and integration with existing enterprise systems. Kanerika’s FLIP platform powers autonomous AI agents designed for enterprise workflows—schedule a demo to explore your migration path.
Which is better than OpenClaw?
Enterprise-focused agentic AI platforms outperform OpenClaw for production deployments by delivering governance, security, and scalability that OpenClaw’s open-source framework lacks. Platforms with built-in data quality controls, compliance certifications, and dedicated support consistently handle enterprise workloads more reliably. Purpose-built AI agents for specific domains—legal summarization, financial analysis, and document intelligence—also surpass generic OpenClaw implementations in accuracy and speed. The right choice depends on your specific use case and compliance requirements. Kanerika helps organizations identify and implement the optimal AI agent solution—reach out for a tailored assessment.
What is the difference between OpenClaw and enterprise agentic AI platforms?
OpenClaw provides an open-source framework for building AI agents, while enterprise agentic AI platforms deliver production-ready solutions with governance, security, and compliance built in. Enterprise platforms offer managed infrastructure, SLAs, dedicated support, and pre-built integrations with business systems like ERP and CRM. OpenClaw requires significant development effort for security hardening, audit logging, and scalability. Enterprise solutions also include role-based access controls, data lineage tracking, and regulatory compliance features absent in OpenClaw’s base framework. Kanerika’s enterprise AI solutions bridge this gap with autonomous agents built for compliance—let us show you the difference.
How do I migrate from OpenClaw to a more powerful AI agent framework?
Migrating from OpenClaw starts with auditing existing agent workflows, identifying dependencies, and mapping them to your target platform’s capabilities. Extract custom prompts, tool configurations, and integration logic before selecting an enterprise agentic AI framework that supports your use cases. Plan parallel testing environments to validate agent behavior before cutover. Prioritize platforms offering migration tooling and professional services to minimize disruption. Document agent performance baselines to measure improvement post-migration. Kanerika’s migration specialists have executed complex AI platform transitions with zero downtime—contact us for a free migration assessment.
How do enterprise AI agents handle sensitive data securely?
Enterprise AI agents secure sensitive data through encryption at rest and in transit, automated PII redaction, role-based access controls, and comprehensive audit logging. Advanced platforms implement data isolation boundaries, ensuring agent operations never expose confidential information across tenant environments. Compliance frameworks including SOC 2, HIPAA, and GDPR are embedded into agent architectures rather than applied as afterthoughts. Tokenization and differential privacy techniques further protect data during agent processing and training. Kanerika’s AI Workforce includes Susan, a PII redactor agent that automatically removes sensitive information—explore our security-first approach today.
Is NanoClaw better than OpenClaw?
NanoClaw offers a lightweight alternative to OpenClaw optimized for resource-constrained environments and edge deployments. While OpenClaw provides broader functionality for complex multi-agent systems, NanoClaw excels in scenarios requiring minimal memory footprint and faster initialization. However, neither framework matches enterprise agentic AI platforms for production security, governance, and support. Your choice depends on deployment context—NanoClaw for lightweight applications, OpenClaw for flexibility, or enterprise platforms for mission-critical workloads. Kanerika evaluates your specific requirements to recommend the optimal AI agent architecture—book a consultation to identify your best fit.
What is the best free alternative to OpenClaw for developers?
LangChain and AutoGen stand out as strong free OpenClaw alternatives for developers building AI agent applications. LangChain offers extensive documentation, active community support, and robust tooling for chain-of-thought orchestration. AutoGen excels at multi-agent conversation patterns and collaborative agent workflows. CrewAI provides another compelling option for role-based agent teams. Each framework has distinct strengths—LangChain for flexibility, AutoGen for agent collaboration, CrewAI for structured team dynamics. Evaluate based on your specific use case requirements. Kanerika helps development teams architect scalable agent solutions—connect with our engineers for technical guidance.
Is OpenClaw part of Claude?
OpenClaw is not part of Claude or developed by Anthropic. OpenClaw is an independent open-source AI agent framework, while Claude is Anthropic’s large language model. Developers can integrate Claude as a foundation model within OpenClaw workflows, but they are separate projects with different purposes. OpenClaw orchestrates agent behavior and tool usage, whereas Claude provides the underlying reasoning capabilities. Many agentic AI platforms support multiple LLMs including Claude, GPT-4, and open-source models for flexibility. Kanerika’s AI solutions integrate with leading foundation models—discuss your architecture requirements with our team.
What is the difference between OpenClaw and NemoClaw?
OpenClaw focuses on general-purpose AI agent orchestration with broad flexibility, while NemoClaw specializes in NVIDIA’s ecosystem integration for GPU-accelerated agent workloads. NemoClaw leverages NVIDIA NeMo framework optimizations for faster inference and training on NVIDIA hardware. OpenClaw offers broader model compatibility but lacks NemoClaw’s hardware-specific performance benefits. Choose NemoClaw for high-throughput, GPU-intensive agent deployments; select OpenClaw for platform-agnostic implementations. Enterprise alternatives combine both flexibility and performance optimization. Kanerika architects AI agent solutions optimized for your infrastructure—schedule a technical consultation to explore your options.