As Microsoft Copilot becomes a core part of Microsoft 365, organizations are seeing major productivity gains. From drafting emails to summarizing complex data, Copilot is changing how we work, saving time and boosting efficiency. However, as with any powerful tool, businesses must address Microsoft Copilot security concerns to ensure that sensitive data is protected, and compliance standards are met.
Recent innovations, like Agent Flows in Copilot Studio, further expand Copilot’s capabilities. While Microsoft has embedded strong security features within Copilot, organizations must remain proactive. By understanding and managing potential risks such as data access, privacy, and user behavior, user can confidently embrace the power of AI without sacrificing security.
In this blog, we’ll explore the key security considerations of Microsoft Copilot and provide actionable best practices to help businesses securely implement it, ensuring sensitive information stays protected.
What is Microsoft Copilot?
Microsoft Copilot is an AI tool embedded into Microsoft 365 apps—Word, Excel, PowerPoint, Outlook, and Teams. It helps user complete tasks faster by offering suggestions, generating text, and performing repetitive tasks. For example, you can tell Copilot to compose an email instead of creating one from scratch. As a result, it saves time and reduces the effort needed for everyday work.
What makes Copilot even more powerful is its seamless integration into the tools you use every day. It can rewrite a paragraph, check grammar in Word, explain a formula, or surface insights from data in Excel. Moreover, it keeps learning over time, so its help improves the more you use it.
Source : Microsoft
Security Concerns with Microsoft Copilot
Microsoft Copilot, integrated into Microsoft 365 applications, offers significant productivity benefits but also introduces notable security and privacy risks. Below is a detailed breakdown of the primary concerns:
1. Data Protection and Privacy
Security Concern:
Copilots can access and summarize sensitive information such as emails, documents, and spreadsheets. Poor access controls can expose sensitive data such as internal financial details or personal records to unauthorized users. Moreover, external queries issued by Copilot can inadvertently expose sensitive information.
Mitigation:
Ensure proper access controls are in place to limit who can access sensitive information. You should periodically audit user permissions and apply data loss prevention (DLP) policies. Limit external interactions such as web queries and log any outbound data requests for signs of exposure.
Transform Your Business with AI-Powered Solutions!
Partner with Kanerika for Expert AI implementation Services
2. Prompt Injection Attacks
Security Concern:
Hackers can exploit prompt injection techniques, inserting hidden commands into emails or documents processed by Copilot. These malicious commands could trigger Copilot to perform unauthorized actions, such as retrieving sensitive emails or summarizing confidential documents.
Mitigation:
To reduce the risk of prompt injection, regularly train employees on the importance of secure document handling and validating content before sharing. Implement input validation and security measures to detect and prevent malicious code injections.
3. Over-Permissioned Access
Security Concern:
With the addition of Agent Flows and other new agents in Copilot Studio, the scope of what Copilot can do expands significantly. However, this also increases the risk of over-permissioned access, where Copilot may gain access to data that isn’t necessary for a user’s role.
Source : Microsoft

Mitigation:
Role-based access control (RBAC) should be used, which limits data access according to a user’s role. User permissions should be contained on a need-to-know basis and require regular auditing to align with job functions. Enforce the least privilege principle, ensuring that Copilot only accesses what is required for the user to perform their job.
4. Flawed Data Classification
Security Concern:
Microsoft Purview’s sensitivity labels are crucial for protecting sensitive data. However, Copilot-generated content may not always inherit these labels correctly, leaving unprotected data exposed. Mislabeling files or inconsistent classification can lead to data breaches.
Mitigation:
Ensure that sensitivity labels are applied consistently across all documents, including those generated by Copilot. Use Microsoft Purview to enforce classification policies and audit Copilot’s document creation process to make sure it inherits the correct protections.
5. Amplification of Existing Security Weaknesses
Security Concern:
Copilot doesn’t just retrieve data—it can also summarize and present it. As a result, poorly secured or overlooked content, such as old emails or shared files, may be exposed quickly, even if they were previously forgotten or improperly secured.
Mitigation:
Conduct regular security audits to identify and secure old data or forgotten documents. Implement strict data retention policies and ensure that access controls are consistently enforced across all files, even those less frequently accessed.
6. Intellectual Property Risks
Security Concern:
Copilot’s ability to generate content based on internal data may inadvertently expose proprietary information, trade secrets, or internal strategies. If this generated content is shared externally or stored insecurely, it can lead to intellectual property theft.
Mitigation:
Implement IP protection protocols, including encryption and access controls, to secure Copilot-generated content. Ensure sensitive documents, such as proprietary algorithms or internal strategies, are flagged and protected before sharing or distribution.
7. Overreliance and Lack of Review
Security Concern:
Users may over-rely on Copilot’s AI-generated outputs, taking them at face value without verifying the results. This could lead to the dissemination of incorrect, biased, or incomplete information.
Mitigation:
Promote a culture of verification where employees double-check AI-generated content before acting on it. Encourage critical thinking and provide training on the limitations and potential inaccuracies of AI tools.
Upcoming Webinar: Secure Your AI Environment with Microsoft Purview

As AI tools like Microsoft Copilot become more common in the workplace, understanding how to protect your data is critical. Join our upcoming webinar, “Microsoft Purview for Data and AI,” where leading experts will share insights on building a secure, compliant AI strategy using Microsoft Purview.
Hear from Naren Babu, Head of Data Governance & compliance at Kanerika, who brings over 16 years of experience helping organizations achieve regulatory compliance and data privacy. Alongside him, Pedro Ferreira from Concentric AI will share practical strategies for aligning cybersecurity solutions with business needs.
Register Now — Limited spots available.
Comparison of Microsoft Copilot vs. ChatGPT vs. Google Gemini in Security Concerns
1. Data Protection
Microsoft Copilot: Ensures that prompts and responses are not saved or used to train models. It features encryption for data at rest and in transit and offers commercial data protection with Entra ID for eligible users.
ChatGPT: Uses encryption for data transfer and undergoes annual security audits. It also has a bug bounty program to identify vulnerabilities.
Google Gemini: Emphasizes data privacy with features like data deletion controls, user activity logs, and confidential computing protections for sensitive workloads.
2. Access Controls
Microsoft Copilot: Provides strict access controls through Microsoft Entra ID and integrates with Microsoft 365’s role-based permissions to limit data exposure.
ChatGPT: Implements strict access controls to protect sensitive areas of its codebase and user interactions.
Google Gemini: Offers advanced IAM (Identity and Access Management) recommendations and integrates with Google Workspace for granular access control.
3. Compliance
Microsoft Copilot: Complies with GDPR, HIPAA, and other global standards, ensuring enterprise-grade compliance within the Microsoft ecosystem.
ChatGPT: Lacks specific enterprise compliance certifications but adheres to general privacy principles.
Google Gemini: Operates on Google Cloud, which is known for its robust compliance framework, including certifications like ISO/IEC 27001 and SOC.
Copilot in Microsoft Fabric: Simplifying Data Management with AI
Learn how Copilot in Microsoft Fabric utilizes AI to automate data tasks, enhancing productivity and simplifying data management.
4. Threat Detection
Microsoft Copilot: Uses AI-powered tools to detect insider risks and external threats within the Microsoft environment.
ChatGPT: Relies on its bug bounty program and external audits but lacks specialized threat detection capabilities.
Google Gemini: Integrates Mandiant’s threat intelligence for real-time threat detection and analysis, making it strong in cybersecurity applications.
5. Privacy Concerns
Microsoft Copilot: Accesses organizational data through Microsoft Graph but ensures suggestions are relevant without retaining user inputs beyond diagnostics.
ChatGPT: Collects interaction data for improvement but does not save prompts or responses permanently.
Google Gemini: Provides tools for secure file sharing and document access but has potential risks related to Google Workspace extensions being exploited by attackers.
| Feature | Microsoft Copilot | ChatGPT | Google Gemini |
| Data Protection | Encrypted; no prompt retention | Encrypted; annual audits | Data deletion & activity logs |
| Access Controls | Role-based via Entra ID | Strict internal controls | Advanced IAM & Workspace tools |
| Compliance | GDPR, HIPAA | General privacy principles | ISO/IEC 27001, SOC 2 |
| Threat Detection | AI-powered risk detection | Bug bounty program | Mandiant threat intelligence |
| Privacy | Limited diagnostic data collection | No prompt retention | Risks in Workspace extensions |
What Steps Has Microsoft Taken to Address Security Concerns with Copilot
Microsoft has implemented several measures to address security concerns associated with Microsoft 365 Copilot:
1. Strict Data Privacy and Access Control
- Copilot can only access and show data that the user already has permission to view. It doesn’t go beyond existing access controls. This means it won’t pull in private chats, documents, or emails that the user isn’t supposed to see.
- Microsoft 365’s built-in permissions (like those in SharePoint and Teams) are respected fully. Organizations don’t need to create new permission rules just for Copilot—it follows what’s already in place.
- In cases where teams work across companies or tenants—such as in shared Microsoft Teams channels—Copilot won’t expose anything beyond what the user is allowed to access. This helps reduce accidental data sharing between different organizations.
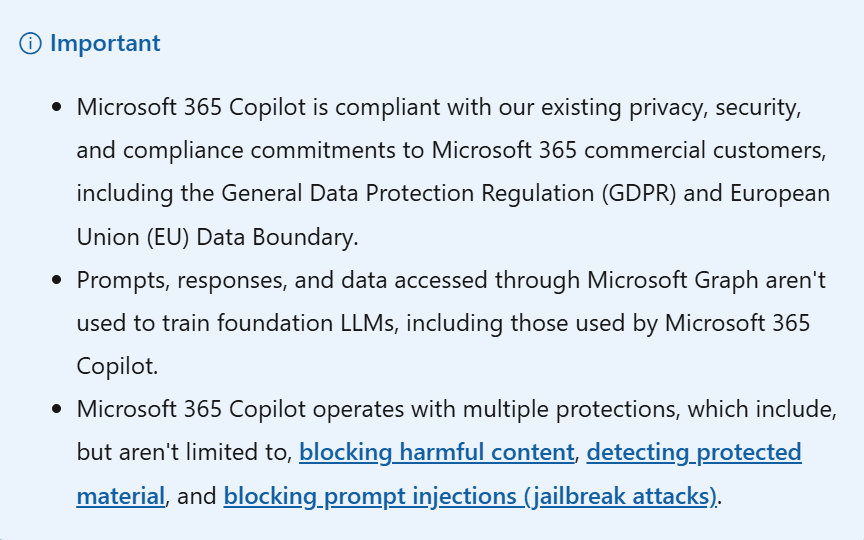
Source: Microsoft
2. No Use of Customer Data to Train AI Models
- Microsoft has made it clear that none of the user prompts, responses, or accessed organizational content is used to train the foundation models that power Copilot.
- The data remains within Microsoft 365’s secure environment. Unlike public tools from OpenAI, Copilot uses Azure OpenAI services, which do not store or reuse customer content for model training.
- This helps prevent your organization’s internal information from being reused in any way outside your environment.
3. Content Filtering to Block Harmful or Unsafe Output
- Microsoft uses a content filtering system that checks both user inputs and AI responses. It works to block anything that falls into categories like hate speech, violence, sexual content, or self-harm.
- These filters are built to recognize and stop content that’s offensive, discriminatory, or inappropriate in any context, even across different languages.
- This helps keep interactions safe and professional, especially in work environments where inappropriate AI responses could cause problems.
4. Protection Against Prompt Injection (Jailbreak Attacks)
- Prompt injection is when someone tries to trick the AI into breaking its rules by using specially written inputs. These attacks can force AI tools to reveal restricted content or behave in unsafe ways.
- Microsoft 365 Copilot is built to defend against such attacks using specialized filters and monitoring tools through Azure AI Content Safety.
- These defenses are designed to catch and block such manipulation before any damage is done.
The Ultimate Databricks to Fabric Migration Roadmap for Enterprises
Explore AI’s impact on robotics and follow our step-by-step guide to efficiently migrate enterprise analytics from Databricks to Microsoft Fabric with minimal disruption.
5. Data Residency and EU Data Boundary Compliance
- Microsoft routes Copilot data to the closest data centers based on the user’s region. For users in the European Union, data is kept inside the EU boundary as much as possible.
- During high usage, data may temporarily move across regions, but safeguards ensure it’s still handled according to EU privacy laws.
- These practices are important for companies that have strict requirements about where their data is processed and stored.
6. End-to-End Encryption
- All data, whether it’s being transferred or stored, is encrypted using methods like TLS, BitLocker, and IPsec. This prevents unauthorized access, even if data is intercepted or stored in the cloud.
- Microsoft uses a layered approach to encryption, meaning even if one system is compromised, additional barriers are in place to keep the data safe.
7. Plugin and Extensibility Controls
- Organizations often use external tools along with Microsoft 365. When Copilot connects with these tools using plugins or Graph connectors, strict rules are in place.
- Only admins can enable or approve plugins. Users can’t just install them on their own. Even when a plugin is used, it can only access data the user is already allowed to see.
- This prevents third-party tools from reaching private or sensitive company data without admin review and control.
8. Activity History and User Data Management
- Copilot keeps a log of user interactions, including prompts and responses. This helps users go back and review what Copilot generated.
- Admins can manage, monitor, or delete this data using tools like Microsoft Purview. They can also apply retention policies to control how long it stays in the system.
- Users also have the option to delete their own Copilot activity history at any time through the My Account portal.
9. Compliance with Global Privacy and Security Laws
- Microsoft 365 Copilot meets global regulations like the GDPR and privacy standards like ISO/IEC 27018.
- These rules are not optional. Copilot’s design is built around them, ensuring that users and organizations stay compliant without needing to take extra steps.
- Microsoft also commits to keeping up with future AI laws as they evolve, especially around transparency and data protection.
10. Responsible AI and Copyright Protection
- Microsoft is working to reduce issues like misinformation, unfair bias, or harmful content in Copilot responses. These areas are part of its Responsible AI standards.
- While users still need to review what Copilot creates, Microsoft provides support and clear guidelines to help users avoid problems.
- If a customer is sued for copyright issues based on Copilot’s output—provided the built-in filters and safety systems were used—Microsoft will step in to defend the customer and cover costs. This is part of their “Copilot Copyright Commitment.
Kanerika: Your Trusted Partner for Strong, Practical Data Governance Solutions
At Kanerika, we know that good data governance is essential for any business that depends on data. With companies making more data-driven decisions than ever, it’s important to manage, protect, and maintain the quality of that data. At the same time, growing concerns around privacy, security, and compliance make it critical to have clear strategies in place for handling sensitive information.
As a trusted Microsoft Data & AI Solutions Partner, we help businesses set up solid data governance systems using Microsoft Purview. Our team has deep experience in deploying Microsoft Purview to create secure, scalable, and regulation-friendly frameworks. This allows our clients to stay compliant, improve data security, and run more efficiently — all while keeping full control over their data.
We also understand that every organization’s data environment is unique. That’s why we take a hands-on approach — assessing your current setup, aligning with your business goals, and customizing solutions that work in the real world. Whether you’re just starting with governance or looking to strengthen an existing setup, Kanerika brings the tools, expertise, and support to get it right.
Empower Your Team with Smart AI Tools for Maximum Efficiency!
Partner with Kanerika for Expert AI implementation Services
Frequently Asked Questions
How safe is Microsoft Copilot?
Microsoft 365 Copilot is built with strong security in mind. It follows Microsoft’s enterprise-grade privacy, compliance, and security standards. Data is encrypted both at rest and in transit. Copilot only shows content the user already has access to, based on Microsoft 365’s permission settings. Also, it doesn’t use your content to train the AI models, which helps protect privacy.
What is the controversy with Microsoft Copilot?
Some concerns have been raised around data privacy, over-permissioning, and potential inaccuracies in AI-generated content. For example, if access controls are not properly configured, Copilot could inadvertently share data not meant for certain users. Despite these concerns, Microsoft has built-in measures to manage permissions, and its ongoing commitment to privacy ensures that businesses can confidently use Copilot while managing these risks effectively.
What are the risks of Copilot for Microsoft 365?
The primary risks include data exposure due to misconfigured permissions, inaccurate AI outputs, and prompt injection attacks where someone might try to manipulate the system. However, Microsoft’s continuous updates and proactive monitoring help mitigate these risks, and the overall benefits of Copilot, such as enhanced productivity, often outweigh these concerns when proper controls are in place.
What are the downsides of Microsoft Copilot?
Although Copilot is incredibly useful, it’s not perfect. It may occasionally provide inaccurate or incomplete answers, particularly when context is limited. Proper setup and user training are essential to avoid these issues. With the right configuration and user awareness, Copilot becomes an invaluable tool that saves time and enhances efficiency.
Can Copilot access my files?
Copilot can only access files that you already have permission to view, so it respects your Microsoft 365 permissions. If configured correctly, Copilot will not gain access to restricted or private content. This ensures that Copilot works within the boundaries of your organization’s data policies, providing assistance while maintaining privacy and security
Is Copilot more secure than ChatGPT?
In enterprise settings, Microsoft 365 Copilot is generally more secure than ChatGPT. Copilot operates within the Microsoft 365 ecosystem and follows strict access controls, ensuring data privacy. ChatGPT, being a public tool, might store user interactions for training purposes unless using its enterprise version. Copilot doesn’t store or use your data for model training, offering peace of mind for businesses using AI.
Does Microsoft Copilot collect data?
Microsoft Copilot logs interaction history to improve user experience, such as remembering past chats. This data is stored securely and is not used to train AI models. You have full control over this data, with the ability to manage or delete it. Overall, Microsoft ensures that any data collected remains under strict privacy and security controls, giving businesses the ability to maintain compliance and transparency.
Is Microsoft Copilot compliant with data laws like GDPR?
Yes, Microsoft 365 Copilot complies with global data privacy regulations, including GDPR and ISO/IEC 27018. Microsoft also ensures data residency options are available for different regions, following its EU Data Boundary commitment. By meeting these strict regulations, Copilot helps organizations stay compliant while offering AI-driven tools to increase productivity.